Essence
A commit-reveal scheme is a cryptographic primitive used to enforce fairness in decentralized systems by preventing participants from exploiting information asymmetry. The core mechanism involves two distinct phases: first, a “commitment” phase where a participant submits a cryptographic hash of their intended action without revealing the action itself; second, a “reveal” phase where the participant broadcasts the actual action and the system verifies that it matches the initial commitment hash. This two-step process ensures that all participants act on a level playing field, preventing strategic front-running or malicious manipulation based on observing pending transactions in an open mempool.
In the context of decentralized options markets, the commit-reveal scheme addresses a critical vulnerability inherent to public transaction broadcasting. When an options order, especially a large one, enters the mempool, its existence and parameters can be observed by validators or high-frequency traders. This allows them to calculate the expected price impact and execute a profitable counter-trade, effectively extracting value from the original order before it is confirmed.
The commit-reveal mechanism neutralizes this threat by requiring all participants to commit their orders before any orders are revealed or executed. This forces simultaneous action and removes the informational advantage of observing pending transactions.
The commit-reveal scheme is a foundational cryptographic technique designed to ensure fair execution in adversarial environments by separating the intention to act from the specific details of the action.
Origin
The theoretical underpinnings of commit-reveal schemes predate blockchain technology by decades, stemming from secure multi-party computation (MPC) and game theory. The concept was formalized in cryptography as a method for simulating simultaneous actions in an asynchronous communication environment. The fundamental problem it solves is the “simultaneous exchange problem” or the “mental poker problem,” where participants need to perform actions (like bidding in an auction or playing cards) without revealing their strategy to others before all actions are locked in.
The application of this concept in blockchain architecture became necessary as decentralized exchanges (DEXs) evolved beyond simple automated market makers (AMMs). Early DEX designs, particularly those based on order books, faced significant challenges with front-running. The transparency of the mempool ⎊ a feature intended to ensure openness ⎊ created an attack vector where high-frequency bots could observe pending orders and execute transactions ahead of them, capturing arbitrage opportunities.
The commit-reveal scheme was adapted from its cryptographic origins to address this specific challenge, offering a solution that preserves the decentralization ethos while mitigating the adversarial dynamics of an open, asynchronous market.

Theory
The theoretical application of commit-reveal schemes in options markets centers on mitigating the risk associated with information asymmetry and the sensitivity of option pricing models to small changes in market data. Options pricing is governed by “Greeks,” which measure the sensitivity of an option’s price to various factors like the underlying asset price (Delta), volatility (Vega), time decay (Theta), and changes in Delta (Gamma).
A front-runner observing a large options order can anticipate the impact on these factors, particularly volatility skew, and execute trades to profit from the price change. The commit-reveal process introduces a delay between a participant’s decision to trade and the execution of that trade. This delay is precisely what eliminates the front-running opportunity.
The process can be modeled as a two-stage game where:
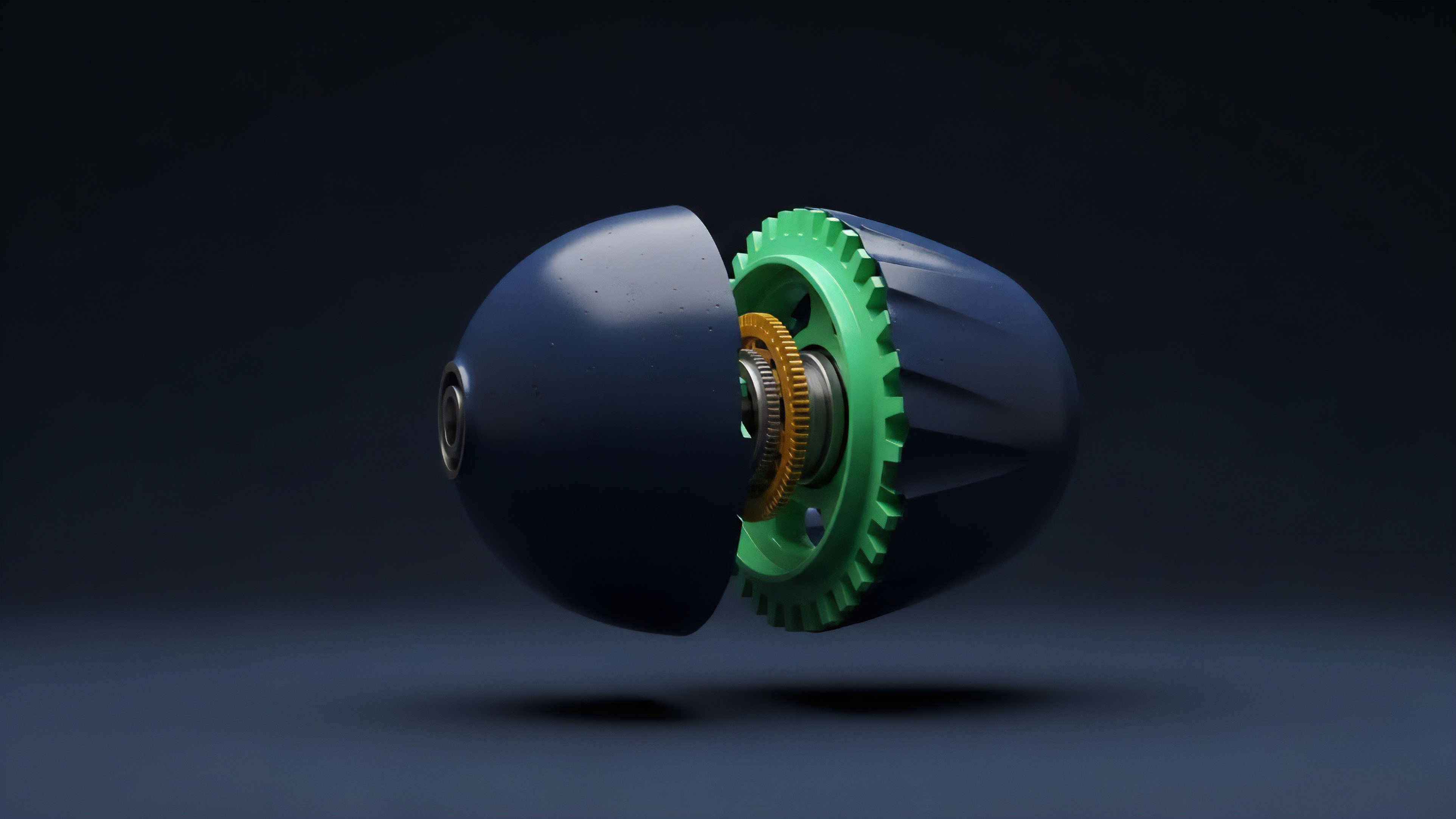
- Commitment Phase: Participants submit a hash of their order (e.g. hash(order_details + salt)). The hash prevents anyone from reconstructing the order details, while the inclusion of a “salt” (a random number) prevents pre-computation attacks where an attacker might try to guess common orders.
- Reveal Phase: After a predetermined time block or number of blocks, all participants reveal their full order details. The system verifies that the revealed orders match the committed hashes. Orders that fail verification are penalized, typically by forfeiting a collateral deposit.
The key architectural decision for a commit-reveal system is the duration of the delay. A longer delay increases security by providing more time for commitments to accumulate, but it also increases the execution risk for the participant. A shorter delay improves execution speed but potentially allows for more sophisticated forms of front-running or market manipulation, especially in high-volatility environments.
The design of an effective system requires careful balancing of these trade-offs, often using a mechanism design approach to align incentives and deter malicious behavior.

Market Microstructure Impact
In traditional financial markets, front-running is prevented by a combination of regulatory oversight and the opaque nature of order books. In decentralized finance, the open mempool creates a unique challenge. A commit-reveal scheme fundamentally alters market microstructure by replacing the continuous, high-speed execution model with a batched, periodic settlement process.
This shift from continuous time to discrete time execution changes how price discovery occurs and how liquidity is managed.
| Mechanism Characteristic | Continuous Order Book (Mempool) | Commit-Reveal Batch Auction |
|---|---|---|
| Execution Speed | Real-time, near-instantaneous execution | Delayed, periodic batch settlement |
| Price Discovery | Continuous based on immediate supply/demand | Discrete based on batch-clearing price |
| Front-Running Risk | High; MEV (Miner Extractable Value) potential | Low; mitigated by simultaneous reveal |
| Capital Efficiency | High for market makers; low for liquidity providers | Lower for market makers due to delay |

Approach
The implementation of commit-reveal schemes in decentralized options protocols presents a set of practical engineering challenges. A primary concern is balancing the security gains with the friction introduced by the delay. The commitment phase requires users to submit a transaction, incurring gas fees.
The reveal phase requires a second transaction, incurring additional fees. This cost structure can make commit-reveal mechanisms economically unviable for smaller, retail-sized options trades, where the transaction cost outweighs the potential front-running risk.

Protocol Specific Implementations
Several protocols have experimented with commit-reveal variants. One common approach involves a “sequencer” or “batcher” contract that collects commitments over a set time period. Once the time period ends, the batch is processed, and the reveal phase begins.
This approach requires careful consideration of the incentive structure for the batcher, ensuring they cannot manipulate the order of transactions within the batch for personal gain. The design of the penalty mechanism for failed reveals is also critical; it must be severe enough to deter malicious actors from committing orders they do not intend to execute, but not so severe that it punishes users for honest network failures or timing issues.
Effective commit-reveal implementation requires a precise balance between security guarantees and capital efficiency, as the two-step process introduces inherent latency and transaction costs.

Challenges in Implementation
A significant challenge arises from the “griefing attack” vector. A malicious actor could commit a large number of orders, then fail to reveal them, effectively spamming the system and preventing legitimate users from participating. To counter this, most protocols require a collateral deposit (a bond) during the commitment phase.
This bond is returned upon successful reveal but slashed if the participant fails to reveal. The optimal bond size must be carefully calibrated to deter griefing without creating excessive capital requirements for legitimate users.
Evolution
The evolution of commit-reveal schemes in decentralized finance reflects a continuous effort to improve efficiency and reduce the friction associated with the initial two-step model.
Early iterations were relatively simplistic, relying on fixed time windows and basic hashing functions. The primary limitation was the trade-off between speed and security; a long delay was secure but created poor user experience, while a short delay risked new forms of manipulation. The most significant advancement involves integrating commit-reveal with more sophisticated cryptographic techniques, specifically zero-knowledge proofs (ZKPs).
ZKPs allow a participant to prove that their revealed order matches their committed hash without revealing the underlying order details to a third party. This adds a layer of privacy to the process, which is particularly relevant for options trading where large positions might reveal a participant’s directional bias. Furthermore, protocols are moving toward hybrid models that combine commit-reveal with other mechanisms.
Some systems utilize commit-reveal for high-value or complex derivatives (like options), while using traditional AMMs or FCFS for simple spot trades. This stratification allows for a more efficient allocation of security resources based on the specific risk profile of the asset or instrument being traded. The goal is to create an “Adaptive Commitment Engine” that adjusts parameters like batch size and reveal window dynamically based on market volatility and order flow characteristics.
Horizon
The future trajectory of commit-reveal schemes points toward a highly specialized and automated architecture. The core challenge in decentralized options markets remains the tension between transparent price discovery and front-running prevention. A purely transparent system allows for efficient pricing but enables predatory extraction of value; a purely commit-reveal system prevents extraction but sacrifices efficiency through latency.

Adaptive Commitment Engine
Our current models for commit-reveal systems are often static. The next logical step involves creating dynamic systems that adjust their parameters based on real-time market conditions. The “Adaptive Commitment Engine” would monitor volatility and liquidity.
During periods of low volatility, the commit-reveal window could be shortened to increase efficiency. During high-volatility events, the window would automatically extend to mitigate the increased risk of front-running and manipulation. This dynamic adjustment requires a robust oracle or data feed that accurately reflects market state without itself becoming a point of manipulation.

Conjecture on Order Flow Segmentation
The primary limitation of current commit-reveal models is that they treat all order flow equally. My conjecture is that optimal efficiency in decentralized options markets will be achieved by segmenting order flow based on risk profile and liquidity. Retail orders, which have minimal price impact, should bypass commit-reveal and go through a low-latency AMM.
Large institutional orders, which carry significant systemic risk, should be routed through a commit-reveal system. The protocol would utilize a dynamic threshold based on order size and market depth to determine the appropriate routing mechanism. This approach minimizes friction for most users while maintaining security for the system as a whole.
Instrument of Agency Adaptive Routing Protocol
The design of a future options protocol should incorporate a smart contract layer that acts as an “Adaptive Router.” This router would analyze incoming order parameters against a set of dynamic thresholds.
- Risk Assessment Module: The module calculates the potential price impact of the incoming order based on current liquidity and volatility. It assigns a risk score to the order.
- Dynamic Threshold Adjustment: The protocol adjusts the risk threshold in real-time. For example, during high-volatility periods, a smaller order might trigger the high-risk pathway.
- Execution Pathway Selection: Orders below the risk threshold are routed to a low-latency, FCFS execution pool. Orders above the risk threshold are routed to a commit-reveal batch auction.
- Incentive Alignment: The batch auction offers better execution prices for large orders, incentivizing institutions to accept the latency, while retail users benefit from lower fees and faster execution.
This stratified approach allows for a more efficient and resilient market microstructure, addressing the specific challenges of options trading in a decentralized environment.

Glossary

Dynamic Thresholds

Order Flow Segmentation
Order Flow Analysis Techniques

Partial Position Reveal
Simultaneous Execution

Incentive Alignment Mechanisms

Verifiable Computation Schemes
Institutional Order Routing

Zero-Knowledge Proof Applications