Essence
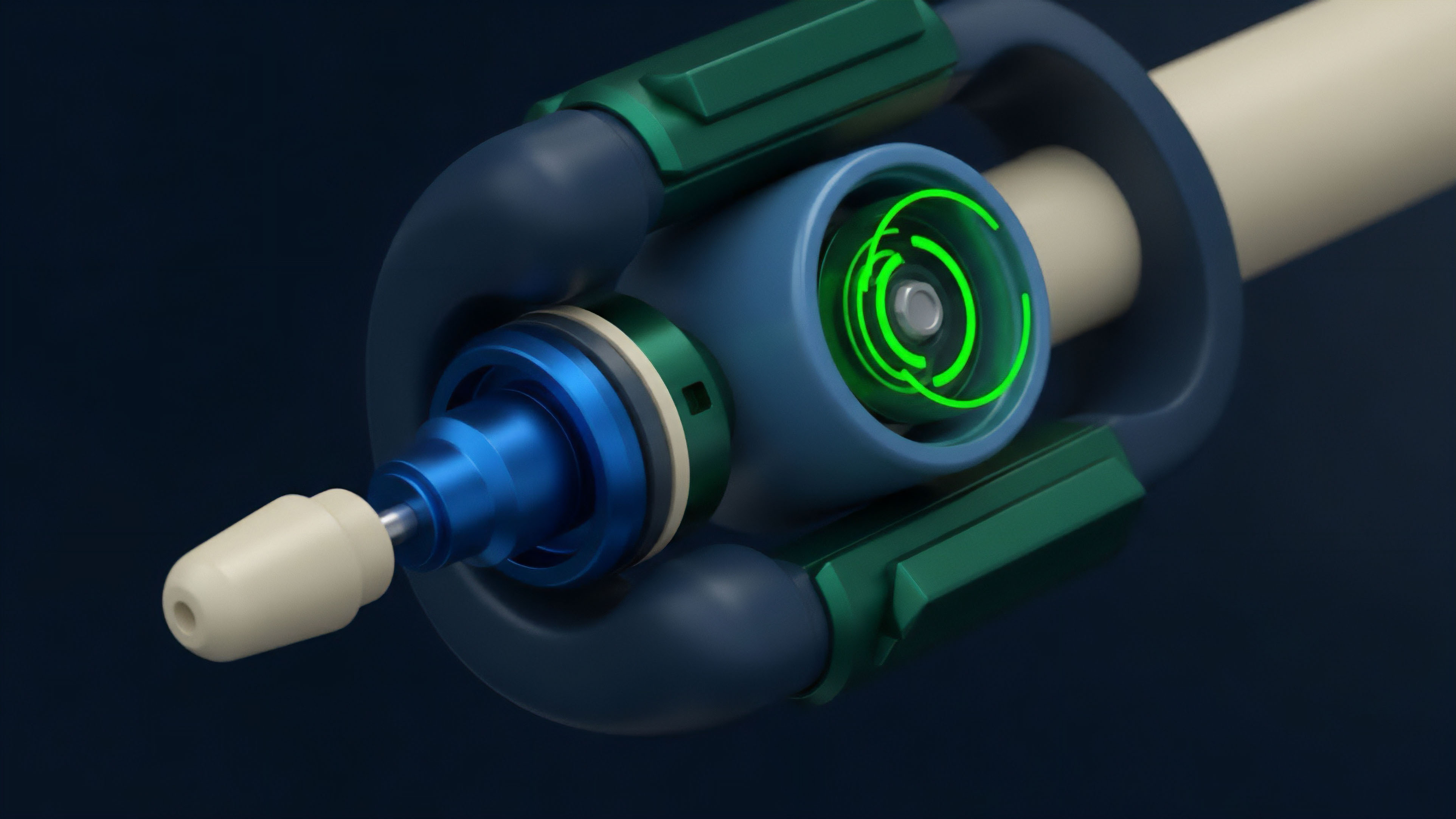
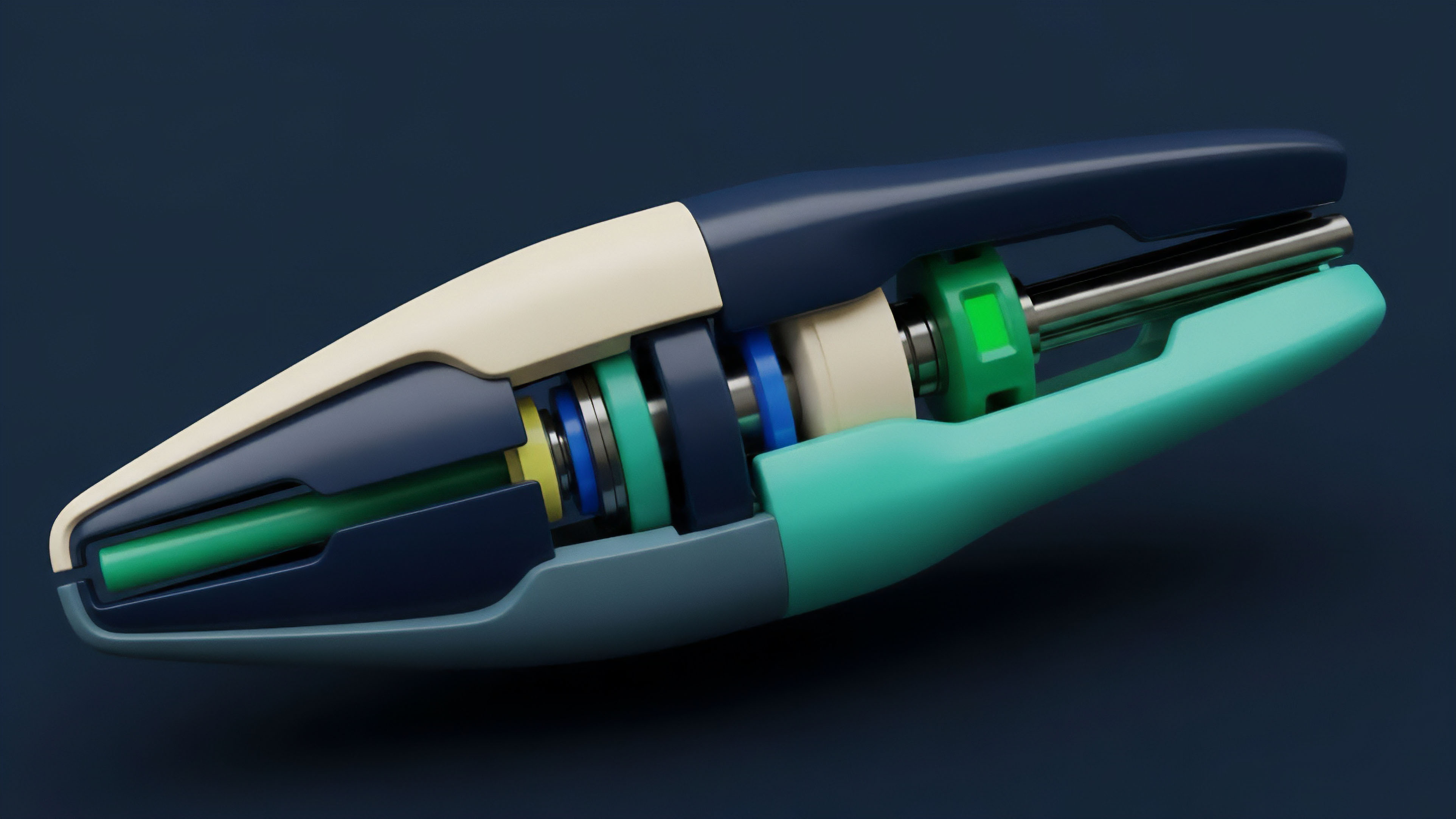
The Reflexivity Engine Exploits represent a class of systemic vulnerabilities arising from the non-linear interaction between market price, investor sentiment, and automated on-chain risk systems ⎊ a destructive feedback loop inherent to leveraged crypto options and derivatives. This is the moment when the market’s psychological state ceases to be a passive observer of price and becomes an active, self-fulfilling driver of volatility. The core mechanism is the acceleration of γ (Gamma) risk through decentralized margin engines.
When a volatile move approaches a cluster of strike prices or liquidation thresholds, the system’s reaction ⎊ automated liquidations, margin calls, or re-hedging ⎊ exacerbates the initial price shock.

Core Vulnerability of Options Liquidity
The fundamental problem lies in the structural illiquidity of decentralized options markets under duress. Unlike spot markets, options require continuous, highly-capitalized market-making to maintain tight spreads and manage risk sensitivity. The reflexivity exploit targets the moment market makers withdraw capital, creating a temporary, profound lack of bid-side depth.
This withdrawal is often a rational response to the sudden, explosive growth in Vega (volatility risk) and Gamma (rate of change of Delta) that precedes a liquidation cascade. The system, designed for efficiency, becomes brittle under stress.
Reflexivity Engine Exploits weaponize the feedback loop between decentralized risk systems and market psychology, turning Gamma risk into a systemic contagion vector.

Systemic Implications
The systemic implication is that the exploitation of a few over-leveraged accounts can be propagated across the entire protocol, affecting even well-capitalized users due to shared liquidity pools or common collateral assets. The exploit is a sophisticated form of adverse selection ⎊ the attacker understands the liquidation queue structure better than the market maker understands the aggregate leverage profile. The options contract, an instrument of precise risk transfer, becomes a catalyst for risk concentration.

Origin
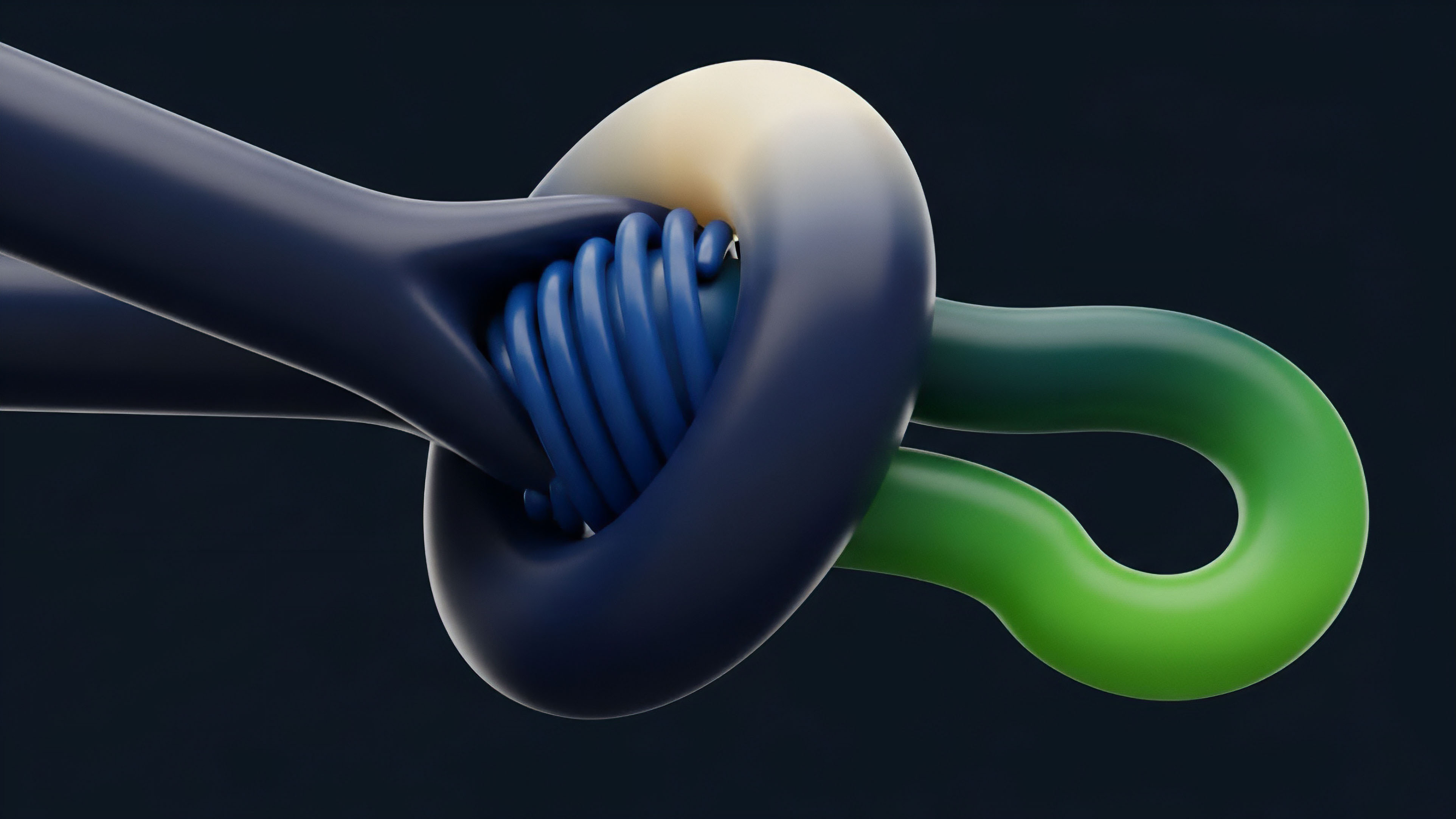
The intellectual origin of this exploit lies in George Soros’s concept of Reflexivity , which posits that participants’ biases and perceptions influence market fundamentals, and those changed fundamentals then reinforce the initial biases. In traditional finance, this process unfolds over months or years. The crypto derivative landscape compresses this timeline to minutes ⎊ or even seconds ⎊ due to the deterministic, low-latency nature of smart contract execution.

The Digital Mutation of Feedback Loops
The transition from human-driven, slow-moving reflexivity to a digital, high-speed exploit is rooted in two architectural components unique to decentralized finance (DeFi):
- Protocol Physics: The invariant properties of the blockchain ⎊ specifically, block time and finality ⎊ set the absolute upper bound on reaction speed. Exploits are often timed to execute within a single block or across a small, contiguous set of blocks, outpacing the off-chain risk management systems of most market participants.
- Smart Contract Determinism: Liquidation functions are public, auditable, and deterministic. An attacker can precisely model the capital requirements, margin health, and execution path of a target position with near-perfect information, a luxury unavailable in opaque, centralized exchanges.
The first documented instances of this behavior were not explicit options exploits but margin liquidation cascades in lending protocols, where a large, strategic loan repayment or withdrawal was used to manipulate the collateral ratio of a target asset, triggering a cascade that netted the attacker a profit through discounted collateral acquisition. The options environment elevates this by adding the non-linear complexity of the Greeks ⎊ the liquidation trigger is not a simple price level but a function of price, time, and implied volatility.
Theory
The quantitative grounding of the Reflexivity Engine Exploit centers on the non-linear risk of the options portfolio under conditions of extreme market stress.
The primary theoretical instrument of the attack is the weaponization of the Implied Volatility (IV) Surface.

Quantifying the Cascade Function
The liquidation function L(P, V, T) in a decentralized options protocol is a step function. The price P is the current spot price, V is the implied volatility, and T is time to expiration. The exploit is successful when a small, targeted capital injection δ C into the spot or options market causes a sufficient shift in P and V to trigger a large-scale liquidation event λ.
The net profit for the attacker, π, is the difference between the discounted collateral acquired and the cost of the initial capital injection, δ C.

Gamma Risk as Ammunition
A core element of the attack is the targeting of high-Gamma, near-the-money options clusters. Gamma is highest for at-the-money options with short time to expiration. As the price moves towards these strikes, the market maker’s δ (Delta) hedge changes rapidly.
If a market maker cannot re-hedge fast enough ⎊ a certainty in a low-liquidity, high-latency environment ⎊ they become a source of instability. The exploit uses this structural γ convexity against the market maker, forcing them into a loss-making re-hedge that further drives the price toward the liquidation threshold.
| Risk Parameter | Traditional Exchange (CEX) | Decentralized Protocol (DEX) |
|---|---|---|
| Liquidation Mechanism | Proprietary, centralized risk engine; human intervention possible. | Deterministic smart contract function; no human intervention. |
| Information Asymmetry | Low (order book visible, margin levels opaque). | High (order book opaque, margin levels auditable on-chain). |
| Reflexivity Speed | Slow (seconds/minutes, dependent on human/HFT reaction). | Fast (sub-block or single-block execution). |
| Exploitable Greek | Theta decay (time value). | Gamma/Vega convexity (volatility/delta change). |

Oracle Latency Vector
The integrity of the liquidation function is contingent on the oracle price feed. An exploit often requires a concurrent manipulation of the oracle’s reference price. By strategically executing large, time-sensitive trades on the reference spot market ⎊ typically a decentralized exchange (DEX) or Automated Market Maker (AMM) ⎊ the attacker can temporarily skew the oracle price, pushing positions past their margin limits before the next oracle update can correct the feed.
This is not a classic front-running of a transaction, but a front-running of the system’s risk check mechanism.

Approach
The execution of the Reflexivity Engine Exploit is a multi-stage, high-capital maneuver that requires both on-chain and off-chain intelligence. The approach is a masterclass in market microstructure analysis, focusing on the friction points between the continuous nature of price discovery and the discrete nature of block execution.

Exploit Execution Phases
The successful attack follows a precise sequence, a strategic interaction with the protocol’s consensus mechanism:
- Target Identification: Identify clusters of high-leverage, short-term options positions, particularly those written against volatile or low-liquidity collateral, using on-chain analytics to map the protocol’s margin health distribution.
- Liquidity Isolation: Use strategic, often flash-loan-funded, trades to temporarily drain liquidity from the spot market or the options AMM’s pool, making the price movement required for the liquidation cheaper and the market maker’s re-hedge impossible.
- Price Perturbation: Execute a large, directional trade on the spot market that feeds the oracle, pushing the price towards the target liquidation cluster. This is the δ C injection.
- Liquidation Trigger and Acquisition: As the protocol’s deterministic function executes the liquidation, the attacker’s pre-positioned bot instantly bids on the discounted collateral, completing the cycle and capturing the systemic value created by the cascade.

Behavioral Game Theory in Action
The exploit is fundamentally a game against other participants ⎊ the market makers and the liquidation bots. It leverages the Harsanyi Transformation , converting a game of incomplete information (no one knows the exact leverage of all others) into a solvable model by making probabilistic assumptions about market behavior. The attacker assumes that under a sudden, sharp move, other market participants will exhibit loss aversion and herd behavior , causing them to panic-sell or withdraw capital, thus accelerating the required price movement.
The exploitation pathway relies on the certainty of smart contract code combined with the uncertainty of human and algorithmic panic, creating an arbitrage window at the intersection of determinism and chaos.
This is a game where the attacker acts as a single, rational, high-capital player against a distributed, psychologically-driven, and structurally constrained collective. The collective’s behavioral bias ⎊ its predictable overreaction to sudden volatility ⎊ is the source of the exploit’s alpha.
Evolution
The evolution of the Reflexivity Engine Exploits has tracked the increasing sophistication of DeFi protocols.
Early attacks were clumsy, relying on simple flash loan oracle manipulation. The current generation of exploits is far more subtle, targeting second-order effects like funding rate volatility in perpetual futures or the cross-protocol margin effects of shared collateral assets.
Defenses and Countermeasures
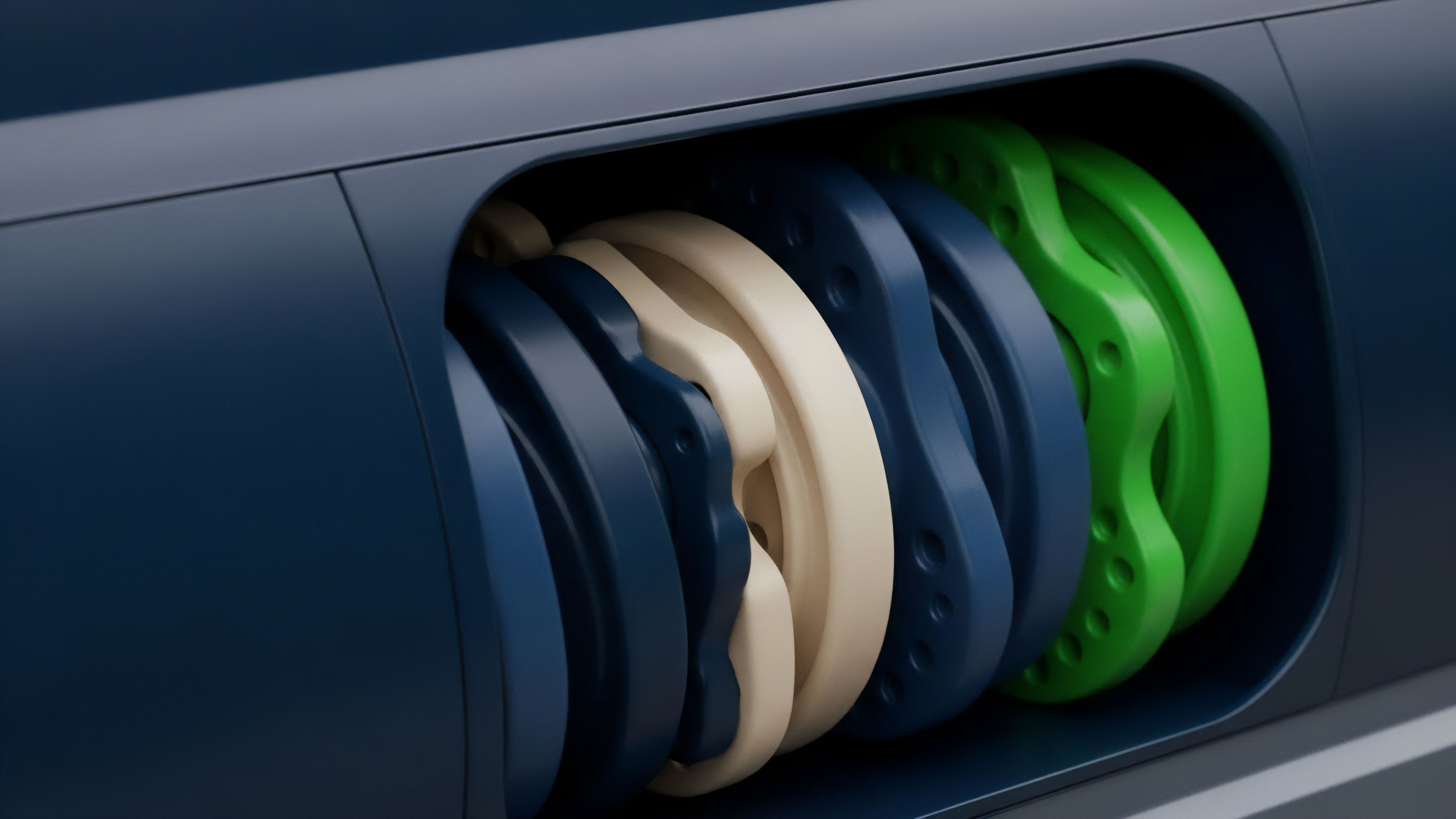
The industry response has been a shift from simple, static risk parameters to dynamic, systems-based defenses. The initial response was to increase collateral ratios ⎊ a naive approach that only reduced capital efficiency without addressing the root cause. The advanced countermeasures now center on dampening the reflexive feedback loop:
- Decentralized Circuit Breakers: Implementing temporary trading halts or automated, time-decaying margin surcharges when volatility or liquidation volume exceeds a pre-defined threshold. This is a deliberate attempt to inject friction and slow the block-by-block execution of the cascade.
- Dynamic Margin Requirements: Using volatility forecasting models, often GARCH-based, to adjust the initial and maintenance margin requirements based on realized and implied volatility, thereby forcing users to de-leverage before a high-Gamma cluster is reached.
- Liquidation-Agnostic Oracles: Moving away from single-source DEX feeds toward time-weighted average price (TWAP) oracles aggregated across multiple venues. This raises the cost of the initial price perturbation δ C to an economically unviable level for most attackers.
The Regulatory Arbitrage Angle
While not a direct part of the exploit, the lack of a unified regulatory framework allows these exploits to persist. A protocol that would be subject to strict capital requirements and market manipulation oversight in a traditional jurisdiction can operate globally without these constraints. The attacker is arbitraging not just price, but the cost of systemic risk ⎊ transferring the cost of their profit onto the decentralized community and market makers.
This is where the pragmatic strategist sees the greatest long-term threat ⎊ unmanaged systemic risk will inevitably invite heavy-handed, blunt regulatory intervention.
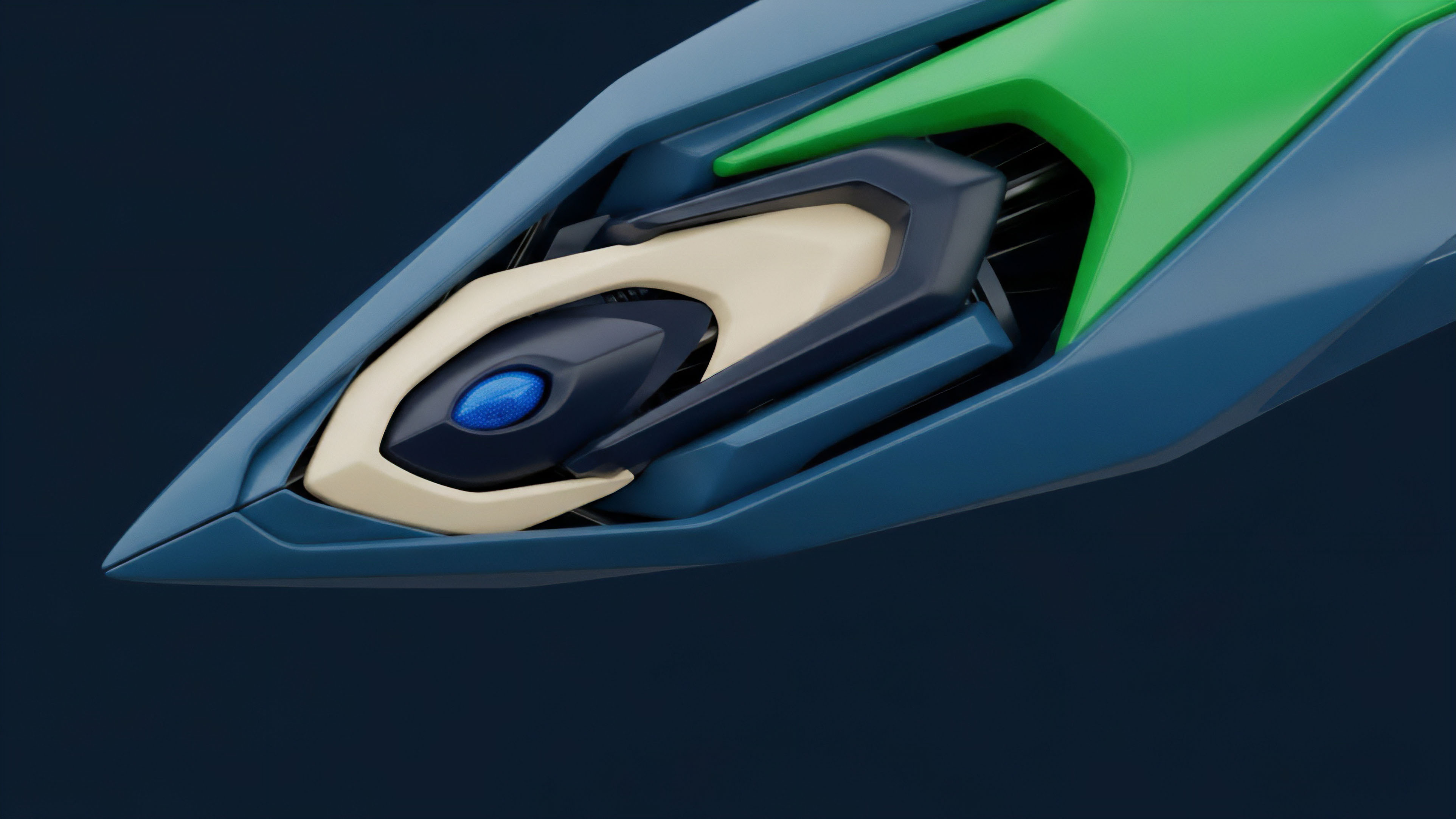
Horizon
The future of the Reflexivity Engine Exploits will be defined by the collision of increasingly sophisticated behavioral models and the emergence of cross-chain risk primitives. As options markets fragment across multiple Layer 2 solutions and different blockchains, the systemic risk becomes harder to track but easier to weaponize.

Cross-Chain Contagion Vectors
The next generation of the exploit will likely target the interoperability layer. An attacker could use a flash loan on Chain A to manipulate the price of a wrapped asset, which is then used as collateral for an options position on Chain B. The oracle on Chain B, receiving a delayed or manipulated price feed from Chain A, triggers a cascade. The attacker profits by simultaneously shorting the derivative on Chain B and acquiring the discounted collateral on Chain A.
| Architecture | Primary Defense Mechanism | Systemic Focus |
|---|---|---|
| Protocol-Agnostic Margin Engines | Shared, transparent collateral pool with unified, real-time risk parameters. | Systemic Risk & Contagion |
| Decentralized Volatility Futures | Creation of a liquid instrument to hedge implied volatility (Vega) across all strikes. | Quantitative Finance & Greeks |
| Verifiable Delay Functions (VDFs) | Injecting cryptographically-enforced, minimum time delays into liquidation processes. | Protocol Physics & Consensus |
The Inevitable Arms Race
The arms race is between the attacker’s ability to model the system’s fragility and the architect’s ability to inject resilience. Our inability to fully predict the second- and third-order effects of our incentive structures means that these behavioral exploits will persist. We must treat every protocol not as a static contract but as a constantly running game theory simulation ⎊ one where the incentive to exploit is always perfectly aligned with the technical capacity to do so.
The solution does not lie in patching code ⎊ it lies in architecting incentive landscapes that make the cost of exploitation prohibitively high. This requires a shift in focus from pure capital efficiency to anti-fragility ⎊ designing systems that improve under stress.
The final defense against the Reflexivity Engine Exploits is not better code, but a superior, anti-fragile incentive design that turns the attacker’s capital against their own probabilistic edge.

Glossary

Market Microstructure Vulnerability

Protocol Resilience against Exploits and Attacks
Game Theory Enforcement

Behavioral Agent Simulation

Market Behavioral Biases

Api Exploits

Behavioral Arbitrage

Game Theory Stability
On-Chain Reflexivity