Essence
Recursive Volatility Shielding represents the transition from reactive liquidation to proactive, algorithmic capital preservation. This structural system functions as a programmable immune response within decentralized financial protocols, utilizing automated derivative strategies to neutralize tail risk. Instead of relying on manual intervention or external market makers during periods of extreme turbulence, these systems embed defensive logic directly into the smart contract layer.
The objective resides in maintaining protocol solvency through self-executing hedges that adjust in real-time to shifting market parameters.

Structural Foundations of Algorithmic Immunity
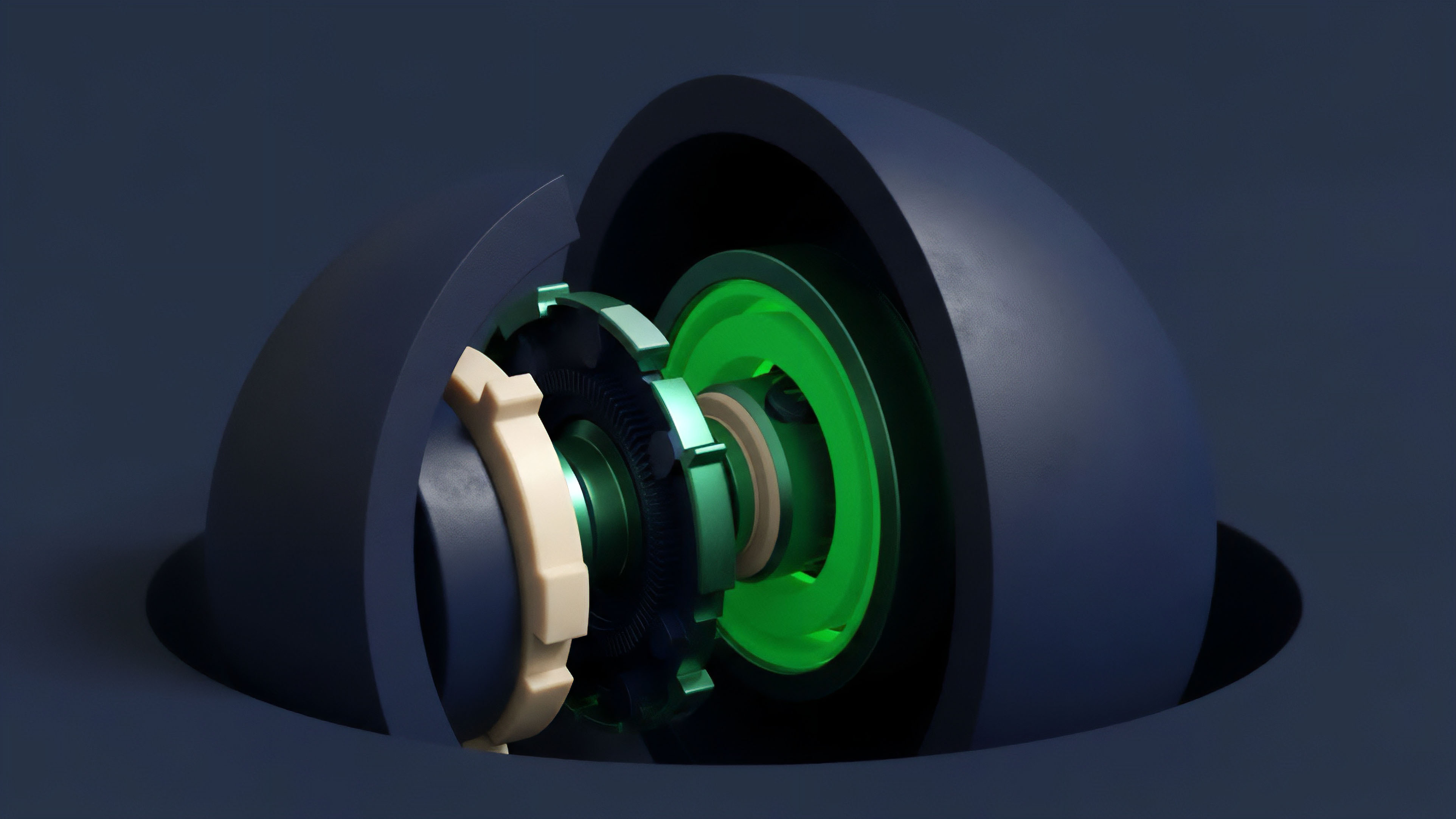
The architecture of a Recursive Volatility Shield relies on the continuous monitoring of on-chain liquidity and price volatility. When specific risk thresholds are breached, the system automatically initiates defensive positions ⎊ typically through the acquisition of put options or the execution of delta-neutral rebalancing. This creates a buffer that protects the underlying collateral from cascading liquidations.
By internalizing the hedging process, protocols reduce their dependence on external liquidity providers who often retreat during high-stress events.
Recursive Volatility Shielding functions as a self-executing immune system for capital, neutralizing tail risk through automated derivative strategies.
Adversarial environments necessitate a shift toward these self-contained defense mechanisms. In a landscape where code is the ultimate arbiter, the ability of a protocol to defend its own balance sheet without human oversight becomes a primary determinant of long-term survival. This logic extends beyond simple collateral ratios, moving into the domain of sophisticated financial engineering where the protocol itself becomes an active participant in the options market to safeguard its users.
Origin
The genesis of autonomous defense resides in the catastrophic failure of traditional liquidation engines during the March 2020 market collapse.
As Ethereum gas prices spiked and liquidity evaporated, many decentralized protocols found their safety mechanisms rendered useless by network congestion. This event exposed the fragility of systems that depend on external actors to maintain solvency. The resulting research shifted toward creating internal, automated buffers that could operate independently of broader market conditions.

Historical Precedents and Catalytic Failures
Early decentralized finance relied on over-collateralization as the sole defense against insolvency. This method proved insufficient when price drops occurred faster than the network could process liquidations. The “Black Thursday” event served as a definitive proof of concept for the mandatory transition toward more robust, derivative-based defense.
Developers began integrating synthetic options and automated hedging vaults to provide a secondary layer of protection that does not require immediate on-chain execution during peak congestion.
The failure of manual liquidation engines during the 2020 collapse necessitated the transition toward internal, automated defense buffers.
These early experiments led to the development of what we now recognize as Autonomous Defense Systems. By studying the failures of centralized clearinghouses and the limitations of early DeFi, architects designed systems that prioritize capital efficiency while maintaining a rigorous focus on risk management. The move from static collateral to kinetic, derivative-backed defense represents a significant shift in the mathematical modeling of protocol safety.

Theory
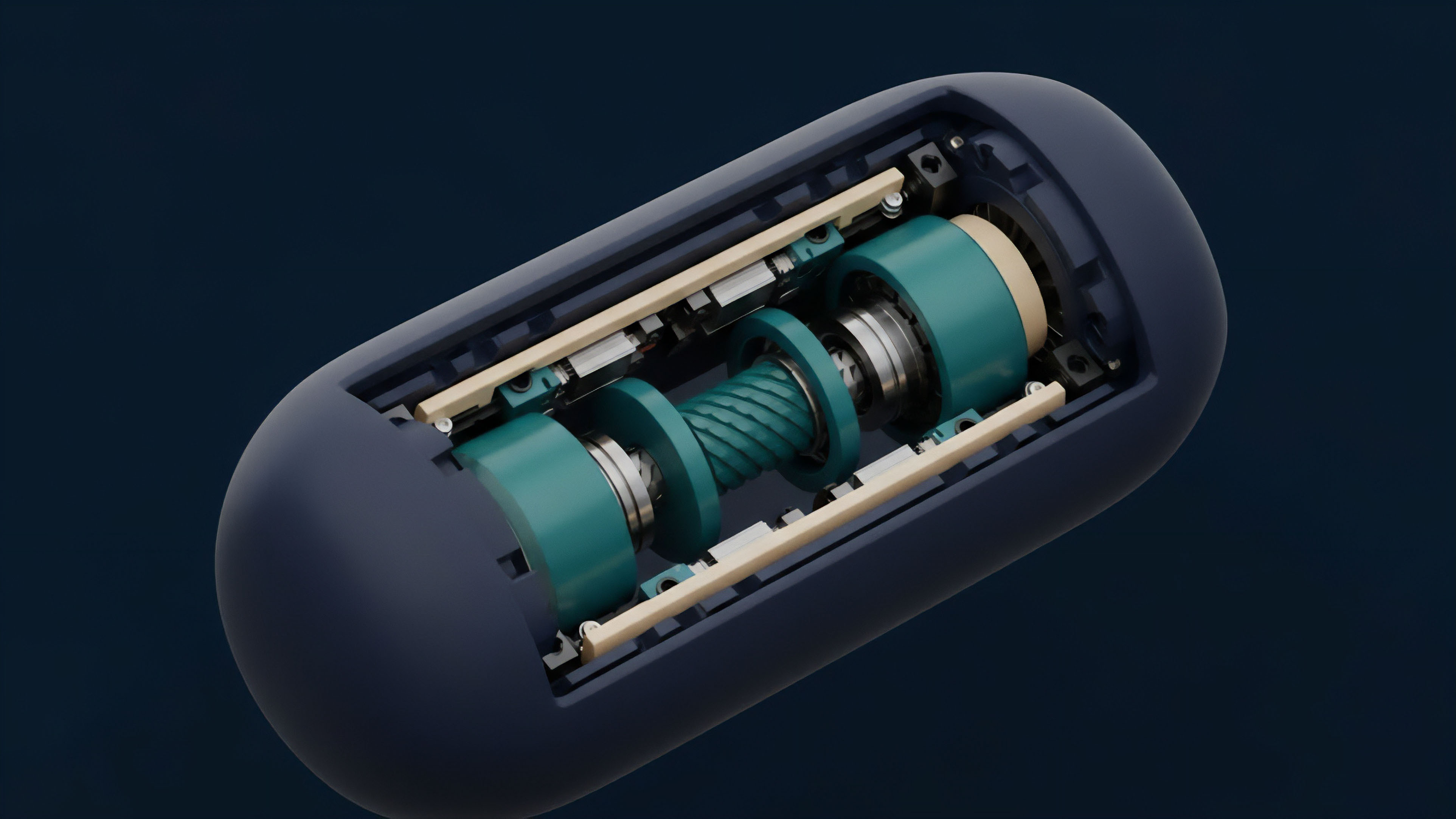
The quantitative foundation of a Recursive Volatility Shield is built upon the continuous management of Greeks ⎊ specifically Delta, Gamma, and Vega.
A protocol employing these systems treats its entire collateral pool as a portfolio that must be hedged against adverse price movements. The mathematical model assumes an adversarial market where participants seek to exploit liquidity gaps. Therefore, the system must maintain a state of “Dynamic Solvency,” where the value of the hedge increases proportionally to the risk of the underlying assets.

Mathematical Modeling of Delta Neutrality
To achieve this, the system calculates the aggregate Delta of all outstanding positions and uses on-chain option markets to offset this exposure. Gamma management is equally vital; as price volatility increases, the rate of change in Delta accelerates, requiring the system to adjust its hedges more frequently. This process is governed by a set of stochastic differential equations that model the probability of a liquidation cascade.
The system’s ability to scalping Gamma ⎊ buying low and selling high during volatile swings ⎊ provides a source of revenue that offsets the cost of the defensive put options. This creates a self-sustaining economic model where the defense mechanism contributes to the protocol’s overall health.
| Risk Parameter | Static Collateral Model | Recursive Volatility Shield |
|---|---|---|
| Delta Sensitivity | Unhedged exposure to price drops | Automated delta-neutral rebalancing |
| Gamma Risk | High risk of liquidation cascades | Proactive gamma scalping and hedging |
| Liquidity Dependency | Relies on external liquidators | Internalized liquidity via options |
| Capital Efficiency | Low (requires high collateral) | High (protected by derivatives) |
The integration of these quantitative strategies requires a high-fidelity connection to on-chain oracles and liquidity pools. If the latency between price movement and hedge execution is too high, the system risks falling behind the market, leading to “slippage-induced insolvency.” Resultantly, the technical architecture must prioritize execution speed and gas efficiency, often utilizing Layer 2 solutions or specialized execution environments to ensure that the defensive logic triggers within a single block of the detected risk event. This level of precision is mandatory for the system to function as intended in a high-frequency trading environment.

Approach
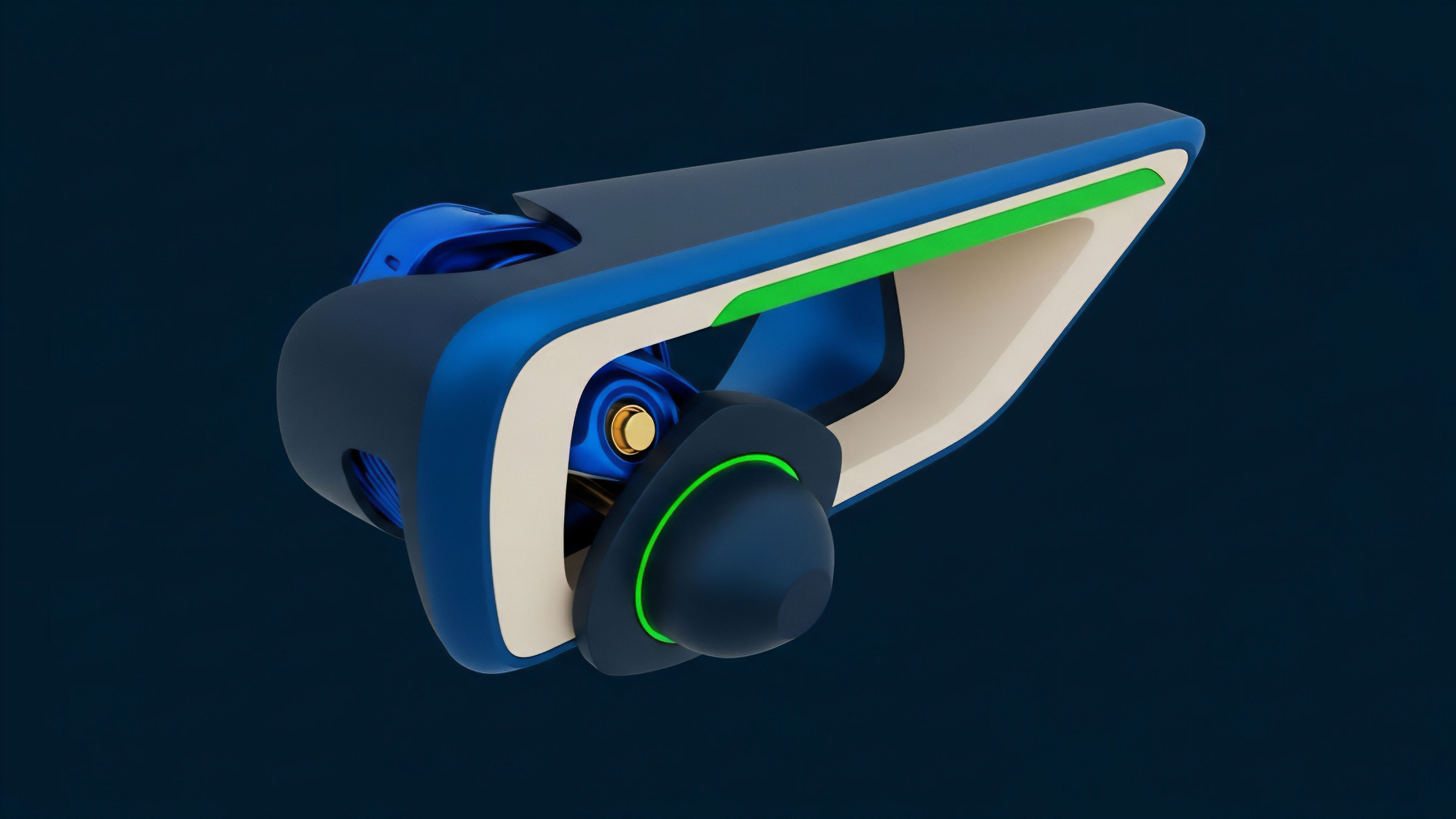
Current methodologies for implementing these systems focus on the creation of “Sentinel Vaults” ⎊ specialized smart contracts that hold defensive assets and execute trades based on pre-defined risk parameters.
These vaults interact with decentralized option protocols to purchase protective puts or sell covered calls, creating a synthetic floor for the protocol’s collateral. The execution logic is typically decentralized through a network of “Keepers” who are incentivized to trigger the defensive actions in exchange for a portion of the protocol’s fees.

Execution Components of Modern Defense
- Risk Oracles: These provide real-time data on price, volatility, and liquidity depth across multiple venues.
- Hedging Engines: Smart contracts that calculate the necessary adjustments to the protocol’s Delta and Gamma exposure.
- Liquidity Aggregators: Systems that source the best prices for defensive options to minimize execution slippage.
- Incentive Layers: Tokenomic structures that reward participants for maintaining the system’s defensive posture.
Sentinel Vaults utilize decentralized option protocols to create a synthetic floor for collateral, ensuring protocol solvency.
Implementing these systems involves a rigorous process of back-testing against historical volatility data and stress-testing under simulated adversarial conditions. Architects must balance the cost of the hedge against the level of protection provided. A hedge that is too expensive will erode the protocol’s competitiveness, while a hedge that is too thin will fail during a true black swan event.
The current methodology favors a tiered defensive strategy, where the intensity of the hedge increases as the protocol approaches its liquidation threshold.
Evolution
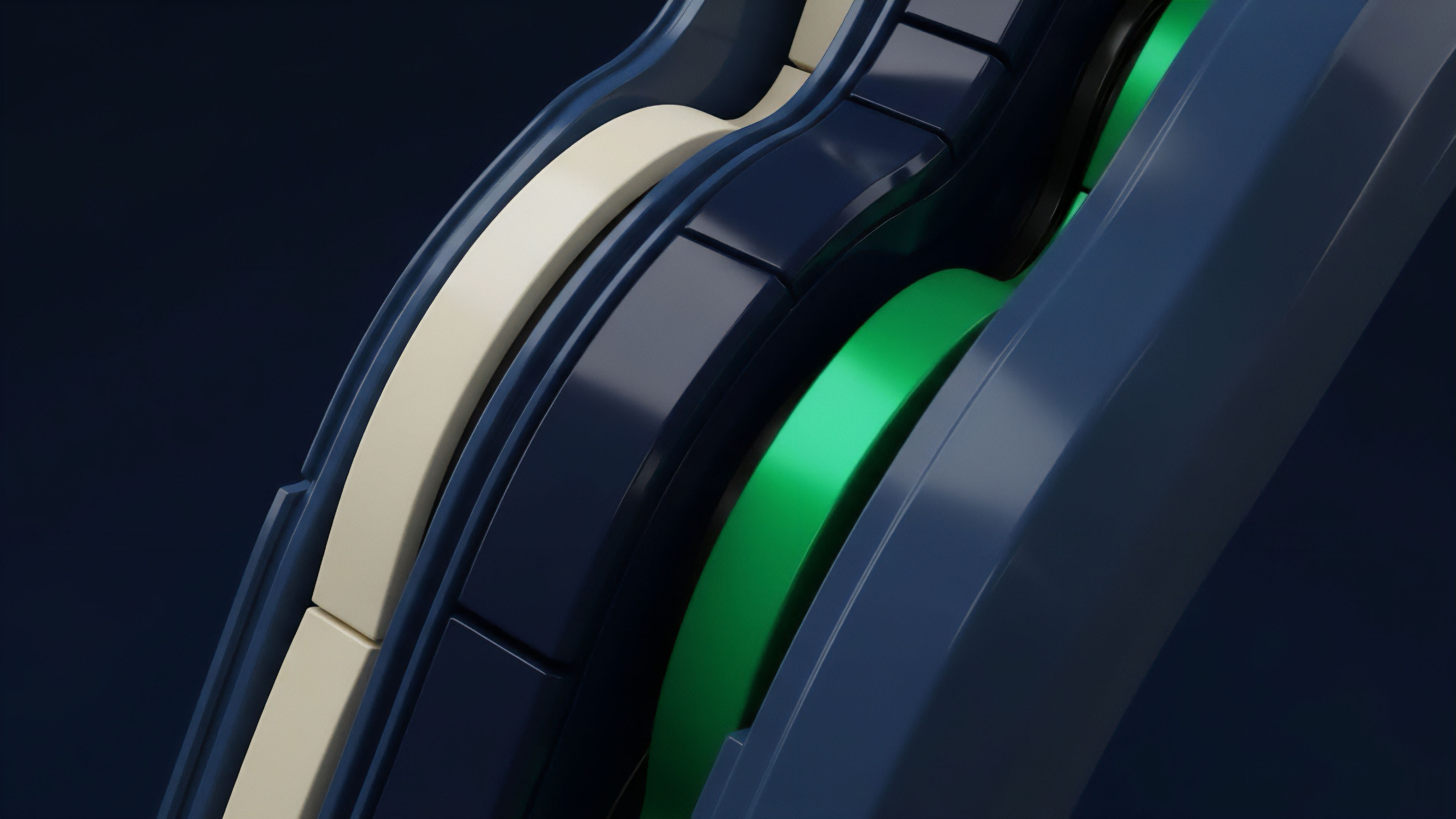
The transition from simple liquidation bots to fully integrated defense systems marks a significant maturation of the crypto derivatives market. Early iterations were often clunky and expensive, consuming large amounts of gas and providing only marginal protection. However, the rise of specialized option protocols and the improvement in on-chain liquidity have allowed for more sophisticated and cost-effective defensive strategies.
This progression mirrors the development of risk management in traditional finance, but at a vastly accelerated pace.

From Reactive Bots to Proactive Systems
| Era | Primary Mechanism | Strategic Focus |
|---|---|---|
| 2018-2019 | Simple Liquidation Bots | Reactive recovery of bad debt |
| 2020-2021 | Automated Vaults | Basic collateral rebalancing |
| 2022-Present | Recursive Volatility Shields | Proactive derivative-based hedging |
The current state of the art involves cross-chain defense mechanisms that can move liquidity between different networks to find the most efficient hedging venues. This prevents the protocol from being trapped on a single congested chain during a market crisis. Additionally, the integration of protocol-owned liquidity has allowed systems to act as their own market makers, further reducing the cost of maintaining a defensive posture.
The focus has shifted from merely surviving a crash to thriving through the volatility by capturing the value created by market dislocations.
Horizon
The future of autonomous defense lies in the integration of predictive modeling and artificial intelligence. Rather than reacting to price movements that have already occurred, future systems will use machine learning to identify the signatures of an impending liquidity crisis. This will allow the protocol to initiate hedges before the volatility spikes, significantly reducing the cost of protection.
These “Predictive Defense Systems” will represent the ultimate evolution of algorithmic risk management.

Future Architectures of Capital Preservation
- Predictive Volatility Modeling: Utilizing off-chain computation to forecast market stress and adjust on-chain hedges proactively.
- Cross-Chain Solvency Synchronization: Maintaining a unified risk profile across multiple blockchains to prevent localized failures.
- Zero-Knowledge Risk Proofs: Allowing protocols to prove their solvency and defensive posture without revealing their specific hedging strategies to competitors.
As these systems become more prevalent, the very nature of market volatility may change. If a significant portion of the market is protected by autonomous shields, the cascading liquidations that characterize crypto crashes could be significantly dampened. This would lead to a more stable and resilient financial system, capable of supporting a much larger scale of economic activity. The ultimate goal is a decentralized financial operating system that is fundamentally immune to the systemic failures of the past, built on a foundation of rigorous mathematics and autonomous execution.

Glossary
Risk Management

Stochastic Risk Modeling
Protocol Physics Validation
Liquidation Cascade Prevention

Recursive Volatility

Delta Neutral Rebalancing

Keeper Network Incentives

Order Flow Toxicity Monitoring
Zero-Knowledge Solvency Proofs