Essence
Automated Market Maker Vulnerabilities represent systemic weaknesses inherent in algorithmic liquidity provision mechanisms where deterministic pricing formulas encounter adversarial market conditions. These vulnerabilities manifest when the mathematical constraints of constant product functions or concentrated liquidity models fail to account for exogenous price shocks, latency arbitrage, or toxic order flow. Participants in decentralized finance rely on these protocols for continuous price discovery, yet the underlying codebases often lack the reactive capabilities of traditional limit order books during periods of extreme volatility.
Automated market maker vulnerabilities arise when deterministic pricing algorithms become decoupled from external market reality during high volatility events.
The architectural fragility stems from the reliance on public, on-chain state updates which create a predictable environment for sophisticated actors to extract value. Liquidity providers face permanent loss when arbitrageurs exploit the discrepancy between the protocol price and broader market indices. This phenomenon forces a re-evaluation of how decentralized exchanges manage capital efficiency versus systemic robustness in adversarial environments.

Origin
The genesis of these vulnerabilities traces back to the initial deployment of constant product market makers, which prioritized censorship resistance and continuous availability over sophisticated risk management.
Early implementations utilized simplistic x y=k equations, providing a foundational mechanism for decentralized trading but ignoring the impact of information asymmetry. Developers initially viewed these systems as closed loops, failing to account for the speed at which external price data influences on-chain arbitrage.
- Latency Arbitrage: Early protocols allowed participants to observe pending transactions in the mempool, enabling front-running of liquidity adjustments.
- Oracle Dependency: Systems relying on single-source price feeds became susceptible to manipulation when the underlying feed failed or exhibited lag.
- Capital Inefficiency: The lack of granular price ranges in initial models necessitated deep liquidity pools to minimize slippage, increasing the surface area for potential exploits.
These early design choices established a trajectory where liquidity provision became a high-risk activity for passive participants. As the sector matured, the shift toward concentrated liquidity models introduced complex mathematical requirements that, while improving capital efficiency, significantly increased the technical burden on liquidity providers to manage their active ranges against rapid price movements.

Theory
The mathematical structure of automated market makers relies on state-dependent pricing, which creates predictable slippage and arbitrage opportunities. When the internal pool price deviates from global benchmarks, arbitrageurs execute trades to restore balance, effectively draining value from liquidity providers.
This process, often termed just-in-time liquidity extraction or sandwiching, exploits the deterministic nature of the pricing curve.
The fundamental risk in automated market maker protocols is the deterministic nature of price discovery which permits arbitrageurs to systematically extract value from liquidity providers.
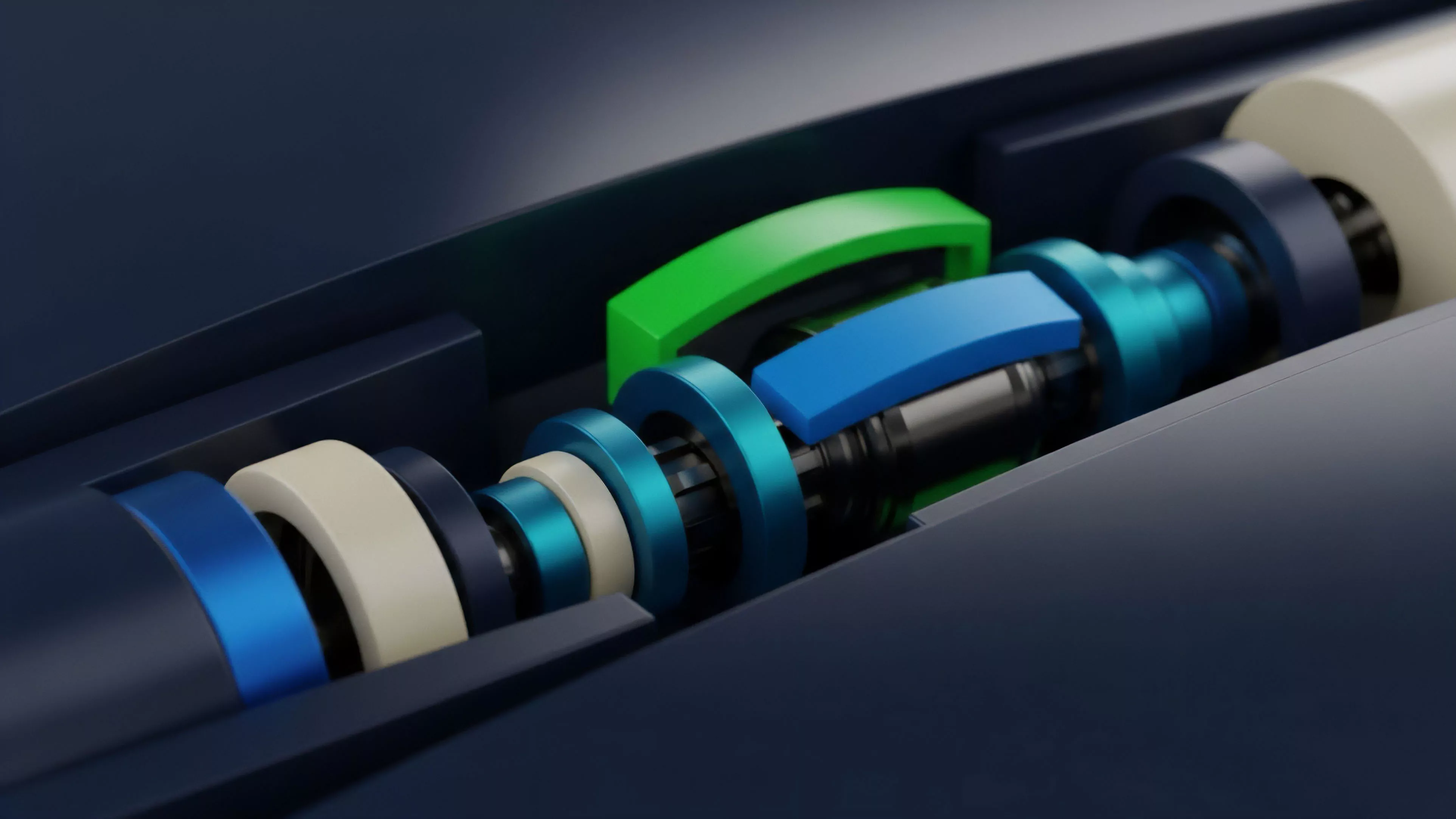
The quantitative modeling of these risks requires analyzing the sensitivity of the liquidity curve to order flow. Practitioners use Greeks, specifically delta and gamma, to quantify how pool exposure changes relative to underlying asset price fluctuations. In concentrated liquidity protocols, the risk is further amplified as liquidity providers essentially write short-term, out-of-the-money options on the asset pair, exposing themselves to significant directional risk during market dislocations.
| Vulnerability Type | Mechanism | Systemic Impact |
| Sandwich Attacks | Front-running order execution | Increased user slippage |
| Toxic Flow | Informed trading against stale prices | Liquidity provider loss |
| Oracle Manipulation | Corrupting price data feeds | Protocol-wide insolvency |
The intersection of game theory and protocol design reveals that these systems are essentially adversarial environments. Participants are incentivized to act against the stability of the pool to capture profit, creating a constant pressure that tests the limits of the underlying smart contract logic.

Approach
Current strategies for mitigating these vulnerabilities involve a combination of off-chain computation and enhanced on-chain validation. Developers are moving away from simplistic pricing models toward hybrid systems that incorporate dynamic fee structures and more frequent oracle updates to keep on-chain prices aligned with global benchmarks.
This transition requires a sophisticated understanding of market microstructure, as liquidity providers now actively manage their positions to minimize exposure to toxic flow.
Mitigation strategies now focus on reducing the window of opportunity for arbitrage through faster price updates and dynamic fee adjustments.
Institutional liquidity providers employ proprietary algorithms to monitor mempool activity, adjusting their positions in real-time to avoid being caught on the wrong side of a price move. This professionalization of liquidity provision has changed the competitive landscape, where success depends on technological speed and the ability to model complex volatility regimes.
- Dynamic Fee Models: Protocols adjust trading costs based on realized volatility to compensate liquidity providers for the increased risk of adverse selection.
- Mempool Monitoring: Advanced agents analyze pending transactions to detect and avoid potentially malicious or toxic order flow.
- Concentrated Range Management: Automated vault strategies actively shift liquidity bands to stay ahead of price trends, reducing the impact of permanent loss.

Evolution
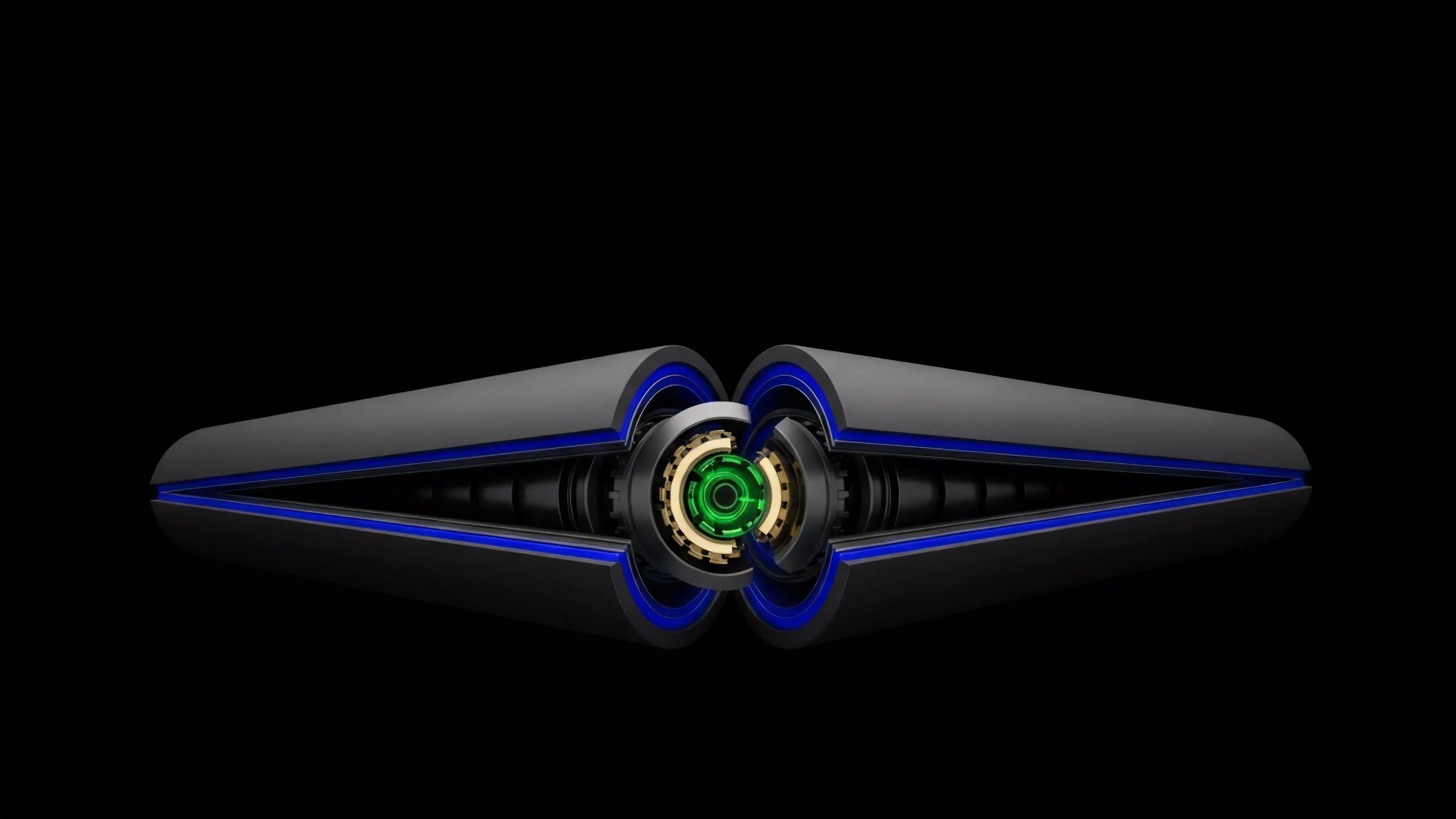
The transition from static liquidity pools to programmable, modular liquidity layers marks a significant shift in how decentralized markets handle risk. We have moved from simple constant product curves to complex, multi-stage protocols that utilize off-chain solvers to execute trades at better prices. This evolution is driven by the necessity to survive in an environment where capital is increasingly mobile and volatility is a constant.
Sometimes I think we are just rebuilding traditional high-frequency trading infrastructure on a blockchain, albeit with different failure modes and trust assumptions. The complexity of these systems has grown exponentially, and with it, the potential for unforeseen systemic failure.
| Development Phase | Primary Focus | Risk Profile |
| Generation 1 | Availability | High arbitrage extraction |
| Generation 2 | Efficiency | Complex directional risk |
| Generation 3 | Resilience | Smart contract complexity |
The current focus is on building robust clearing and settlement layers that can withstand the failure of individual components. This involves decentralizing the order matching process and moving toward off-chain computation to maintain performance while preserving the core benefits of transparency and trustless execution.

Horizon
The future of liquidity provision lies in the integration of zero-knowledge proofs to hide order flow while maintaining verification of trade validity. This advancement will significantly reduce the effectiveness of front-running and other forms of arbitrage that rely on public visibility. Protocols will increasingly adopt machine learning models to predict volatility regimes and adjust pricing curves autonomously, moving closer to truly efficient market discovery. The challenge remains the tension between decentralization and the speed required to compete with centralized venues. We are likely to see the emergence of specialized, high-performance execution layers that function as the backbone for decentralized finance, while user-facing applications become increasingly abstracted from the underlying complexity. The ultimate success of these systems depends on their ability to internalize the risks that are currently externalized to liquidity providers, creating a more stable and sustainable foundation for global asset exchange.