
Essence
Asset Protection Strategies in decentralized finance represent the intentional architectural deployment of cryptographic primitives to secure capital against insolvency, unauthorized access, or systemic collapse. These mechanisms function by isolating risk within specific smart contract layers, ensuring that liquidity remains resilient even when individual protocols experience localized failure. The objective involves maintaining solvency through automated, self-executing risk mitigation rather than relying on external legal recourse or centralized intermediaries.
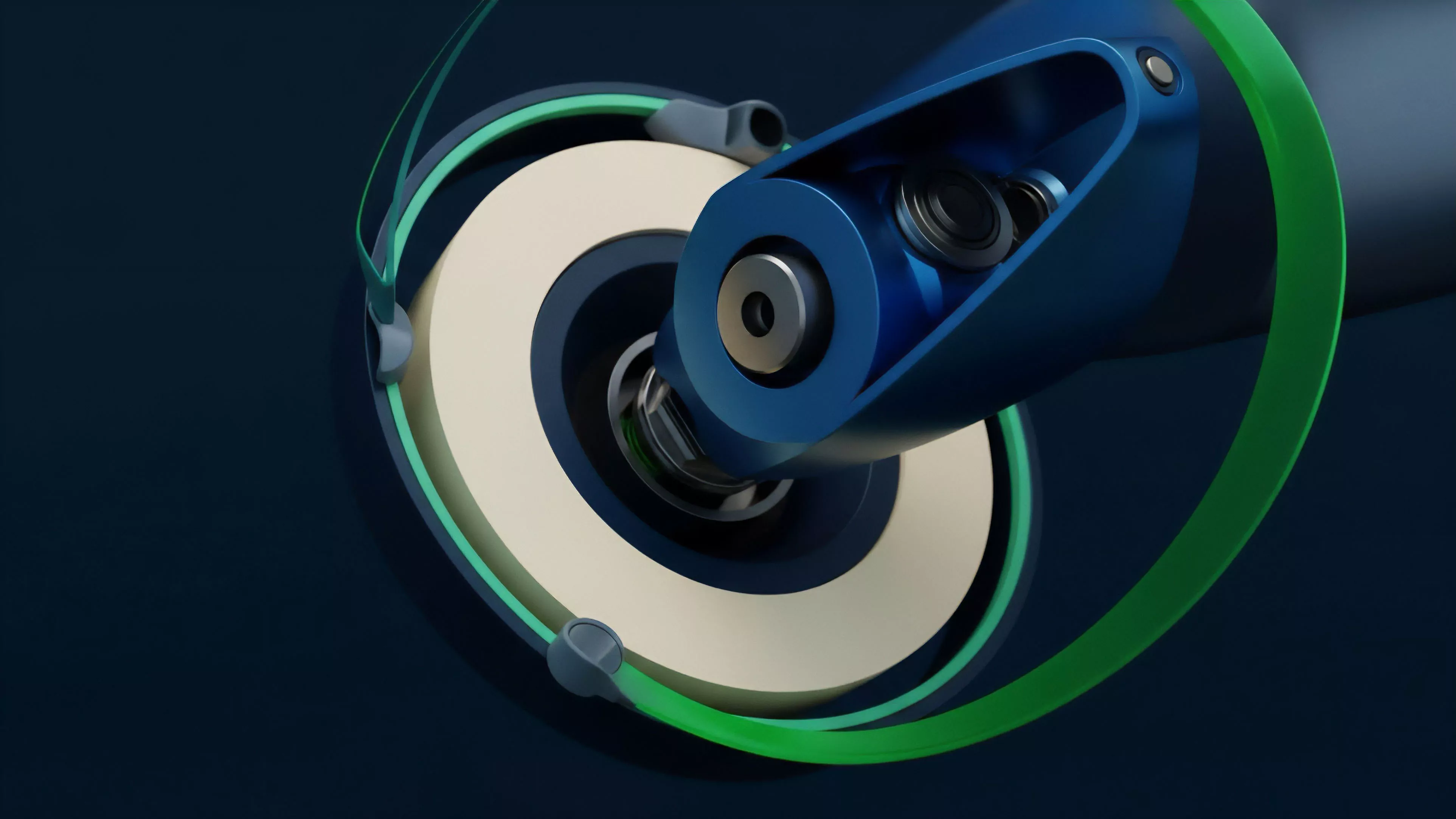
Asset protection strategies utilize cryptographic isolation to maintain capital integrity within decentralized environments.
The structural integrity of these strategies relies on collateralization ratios and liquidation thresholds that operate independently of human intervention. By embedding risk management directly into the protocol physics, these systems create a state where the solvency of a position is mathematically guaranteed by the underlying blockchain state. This shift transforms asset security from a reactive legal process into a proactive technical certainty, fundamentally altering how market participants perceive counterparty risk in permissionless environments.

Origin
The genesis of these strategies stems from the inherent fragility observed in early lending protocols and centralized exchanges. Developers identified that reliance on manual margin calls or human-governed liquidation queues introduced unacceptable latency and corruption vectors. Early iterations focused on simple over-collateralization, where users deposited excess assets to buffer against volatility, establishing a primitive yet effective defense against price fluctuations.
- Automated Market Makers introduced the concept of liquidity pools as a mechanism to stabilize asset availability.
- Smart Contract Escrow enabled trustless custody, ensuring assets remained accessible only under predefined algorithmic conditions.
- Oracle Decentralization provided the necessary data integrity for liquidations to trigger accurately during high volatility.
Decentralized protocols emerged to solve the latency and trust failures inherent in traditional margin management systems.
The transition from manual risk assessment to protocol-enforced solvency marked the maturation of this domain. Early research into game theory and Byzantine fault tolerance provided the mathematical foundation for these systems, ensuring that no single actor could manipulate the liquidation process for gain. This evolution established the current standards for capital safety, prioritizing code-level transparency over institutional promises.

Theory
The mechanics of Asset Protection Strategies are governed by the intersection of quantitative finance and protocol physics. At the center of this framework lies the liquidation engine, a piece of code designed to maintain the systemic health of a lending protocol by closing under-collateralized positions before they reach insolvency. This requires precise mathematical modeling of volatility, often incorporating Greeks ⎊ specifically delta and gamma ⎊ to predict how rapid price shifts impact the probability of default.
| Mechanism | Function | Risk Impact |
| Collateralization Ratio | Minimum buffer requirement | Prevents immediate insolvency |
| Liquidation Threshold | Trigger for position closure | Limits contagion propagation |
| Interest Rate Models | Dynamic borrowing cost | Incentivizes liquidity provision |
Systems risk and contagion represent the primary adversaries. When a protocol fails to liquidate positions with sufficient speed, the resulting bad debt can cascade across interconnected pools. To counter this, advanced strategies employ circuit breakers and dynamic margin adjustments that respond to realized volatility.
The physics of these systems are constantly tested by automated agents seeking to exploit inefficiencies in price discovery or latency in the oracle update cycle.
Systemic health is maintained through automated liquidation engines that respond to volatility-driven risk metrics.
Mathematics acts as the silent arbiter in these adversarial environments. If the cost of liquidation exceeds the value of the collateral, the system incurs a loss that ripples outward, potentially destabilizing the entire protocol. Consequently, the design of these strategies requires a deep understanding of market microstructure, ensuring that the liquidity depth of the underlying assets can support the forced sales required by the liquidation engine.

Approach
Modern implementation of Asset Protection Strategies involves a layered defense, combining on-chain technical controls with off-chain monitoring. Market participants utilize hedging protocols to offset exposure, effectively creating synthetic positions that neutralize the impact of extreme market movements. This approach demands rigorous quantitative analysis, where traders evaluate the probability of liquidation events based on historical data and current order flow dynamics.
- Position Sizing limits the total exposure to any single protocol, mitigating the impact of smart contract exploits.
- Cross-Protocol Collateralization distributes assets across multiple venues to reduce the correlation risk of a single point of failure.
- Real-time Monitoring tools track health factors and trigger automated alerts when positions approach critical thresholds.
Behavioral game theory influences these strategies significantly. Participants often act in concert during periods of high volatility, leading to herd behavior that can exacerbate price crashes. Understanding these social dynamics is as vital as mastering the code.
The successful architect must account for human psychology ⎊ specifically the tendency to panic during liquidation cascades ⎊ and build systems that remain functional even when participants behave irrationally.
Sophisticated strategies combine on-chain liquidation controls with off-chain hedging to mitigate systemic volatility risk.
Technological constraints often dictate the boundaries of these strategies. The speed of block finality and the cost of gas determine how frequently a system can update its risk parameters. When the network is congested, the efficacy of the liquidation engine diminishes, exposing the system to potential losses.
Therefore, modern practitioners focus on optimizing for speed and cost-efficiency to ensure that the protection mechanisms function reliably under peak network stress.
Evolution
The trajectory of these strategies has shifted from basic collateral management to complex, modular risk frameworks. Initial designs focused on single-asset lending, while current architectures support cross-chain collateralization and multi-layered derivative structures. This progression reflects a broader move toward interoperability, where assets move fluidly between protocols, necessitating standardized risk assessment metrics that function regardless of the underlying blockchain environment.
| Development Phase | Core Focus | Primary Challenge |
| Foundational | Simple over-collateralization | Oracle manipulation |
| Intermediate | Liquidity pool stability | Liquidation latency |
| Advanced | Modular risk engines | Systemic contagion |
Regulation remains an evolving variable. As jurisdictional frameworks begin to address decentralized finance, the architecture of these protocols adapts to ensure compliance while maintaining permissionless access. This often leads to the development of privacy-preserving risk assessments, where protocols verify solvency without exposing sensitive user data.
The tension between regulatory requirements and the ethos of decentralization drives innovation in protocol design, pushing developers toward more resilient, self-governing systems.

Horizon
The future of Asset Protection Strategies lies in the integration of artificial intelligence and machine learning to predict volatility with greater precision. Future risk engines will likely move beyond static thresholds, employing predictive modeling to adjust collateral requirements in real-time based on global macro-crypto correlations. This shift toward adaptive systems will allow protocols to maintain stability even during unprecedented market events.
The development of zero-knowledge proofs will further enhance these strategies, enabling protocols to verify the health of complex, multi-layered positions without requiring full transparency of the underlying asset movements. This preserves the privacy of market participants while maintaining the systemic security required for institutional adoption. The goal is a financial architecture that is robust by design, capable of self-correction and continuous improvement in the face of adversarial pressure.
