Zero Knowledge Execution Proofs


Meaning ⎊ Zero Knowledge Execution Proofs provide mathematical guarantees of correct financial settlement while maintaining absolute data confidentiality.
Cryptographic Proof Systems For


Meaning ⎊ Zero-Knowledge Proofs provide the cryptographic mechanism for decentralized options markets to achieve auditable privacy and capital efficiency by proving solvency without revealing proprietary trading positions.
Zero Knowledge Systems


Meaning ⎊ ZKCPs enable private, provably correct options settlement by verifying the payoff function via cryptographic proof without revealing the underlying trade details.
Trusted Execution Environments
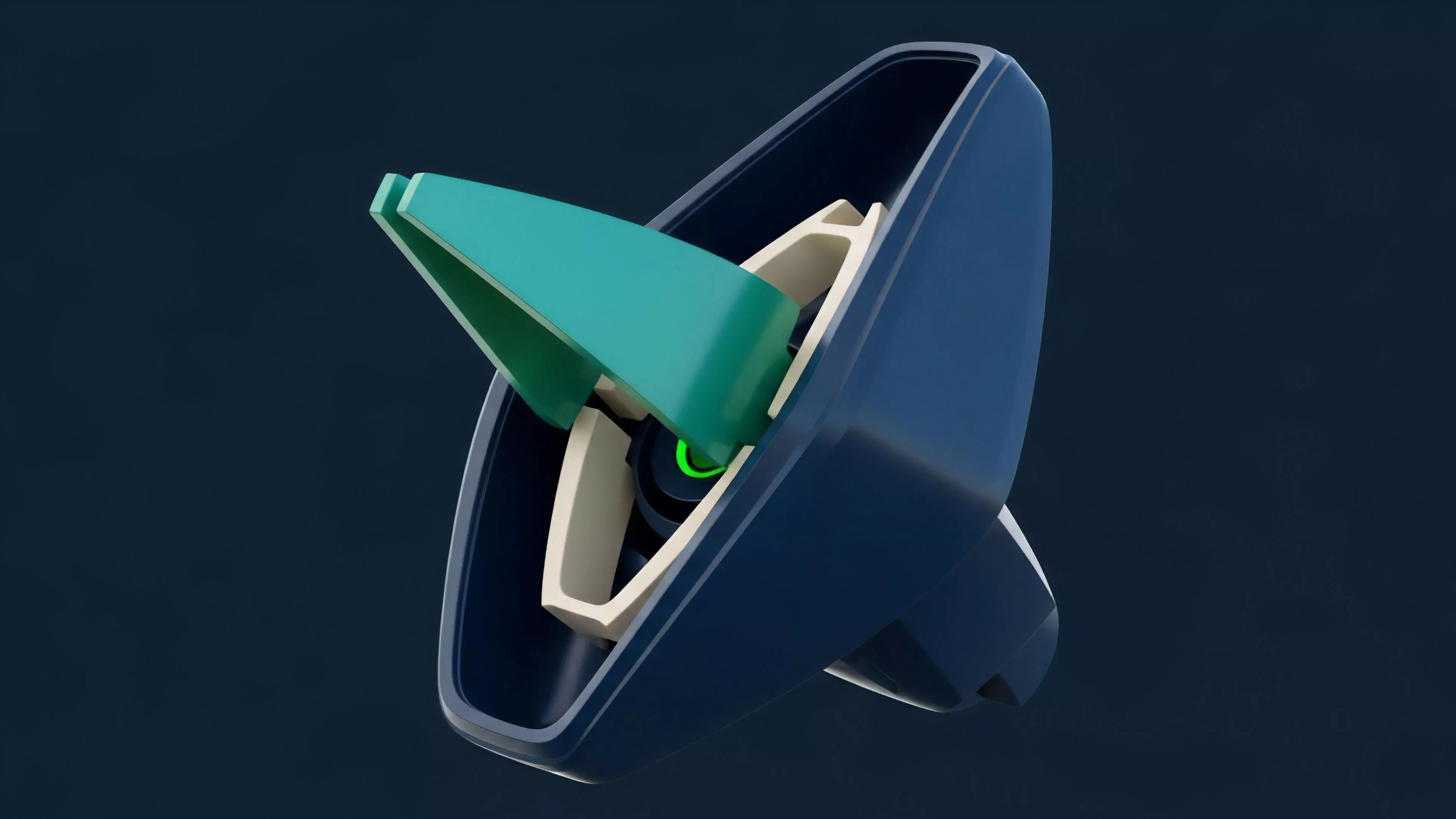
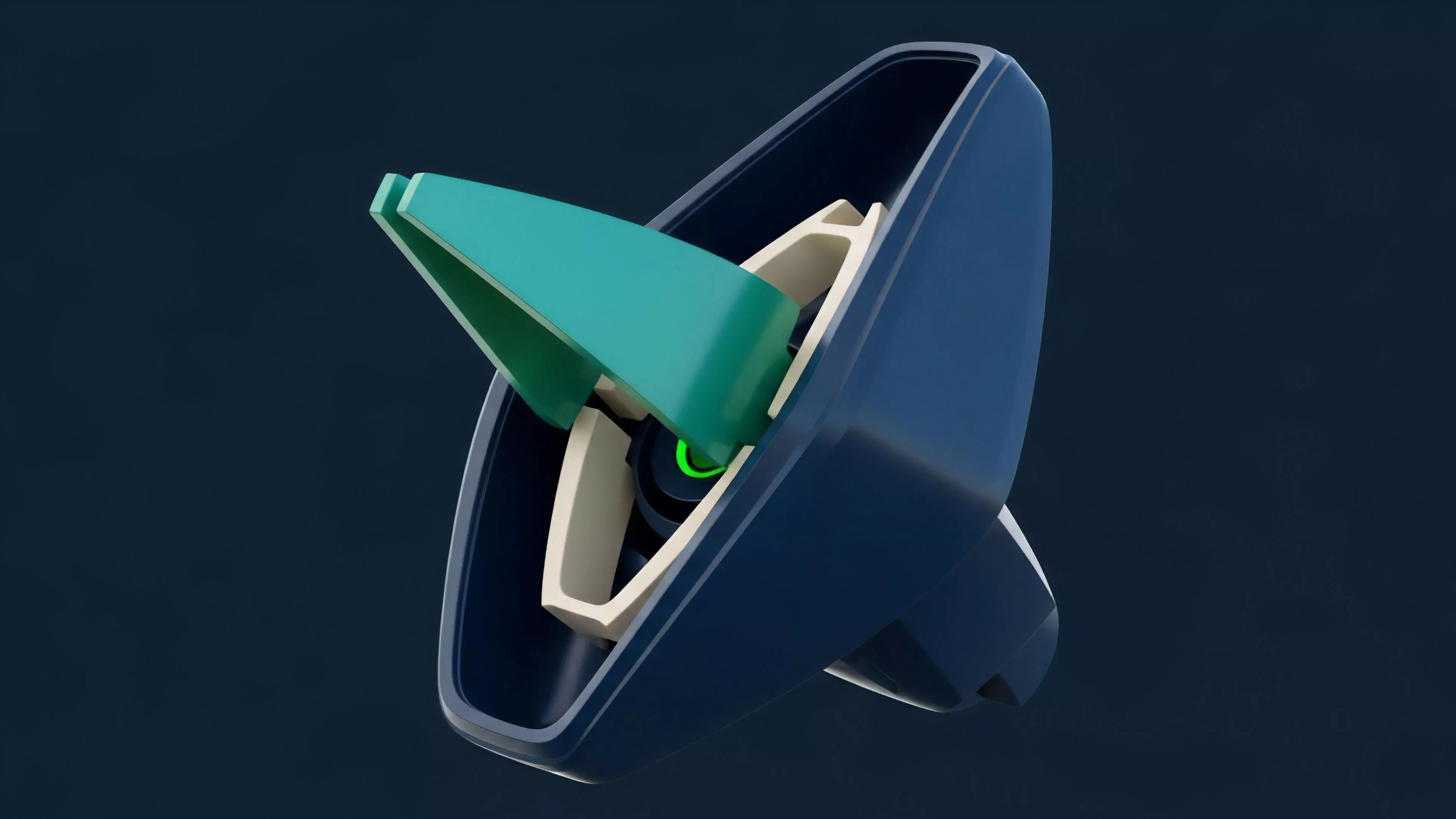
Meaning ⎊ Trusted Execution Environments provide hardware-secured enclaves for off-chain computation, enabling complex derivatives logic and mitigating front-running in decentralized markets.
Trustless Setup


Meaning ⎊ Trustless options settlement provides a framework for managing counterparty risk through automated smart contracts, replacing centralized clearing houses with programmatic enforcement.
Trusted Setup


Meaning ⎊ A Trusted Setup is a cryptographic parameter generation process that enables efficient zero-knowledge proofs for financial applications, introducing a trust assumption that must be mitigated by design.
