Threat Modeling for Wallets


Meaning ⎊ A systematic process to identify potential attack vectors and threats to design an effective security strategy.
Code Audit Protocols


Meaning ⎊ Systematic security review of smart contract code by experts to identify vulnerabilities and flaws before and after deployment.
Emergency Pause Functionality


Meaning ⎊ Circuit breaker mechanism allowing authorized entities to freeze protocol operations during a security exploit or critical bug.
Vulnerability Remediation Standards


Meaning ⎊ Best practices and structured protocols for identifying, reporting, and patching security flaws in digital systems.
Reentrancy Attack Mitigation Logic


Meaning ⎊ Coding practices and mutex patterns preventing malicious recursive function calls during smart contract execution.
Bug Bounty Program Design


Meaning ⎊ Creating structured reward systems that incentivize independent security researchers to report vulnerabilities.
Vendor Security Assessments


Meaning ⎊ Vendor Security Assessments provide the essential framework for verifying third-party resilience, protecting decentralized derivatives from systemic risk.
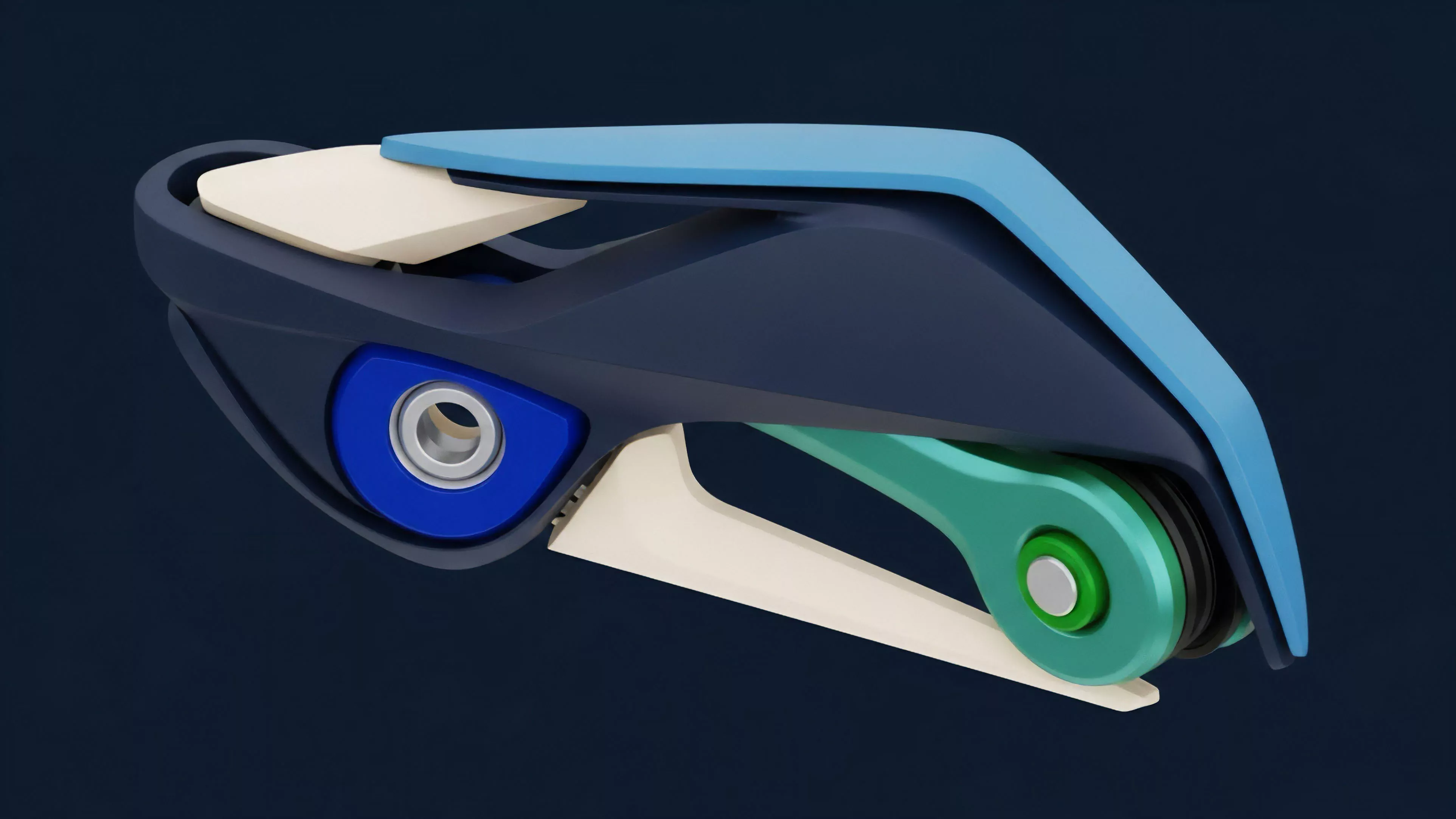
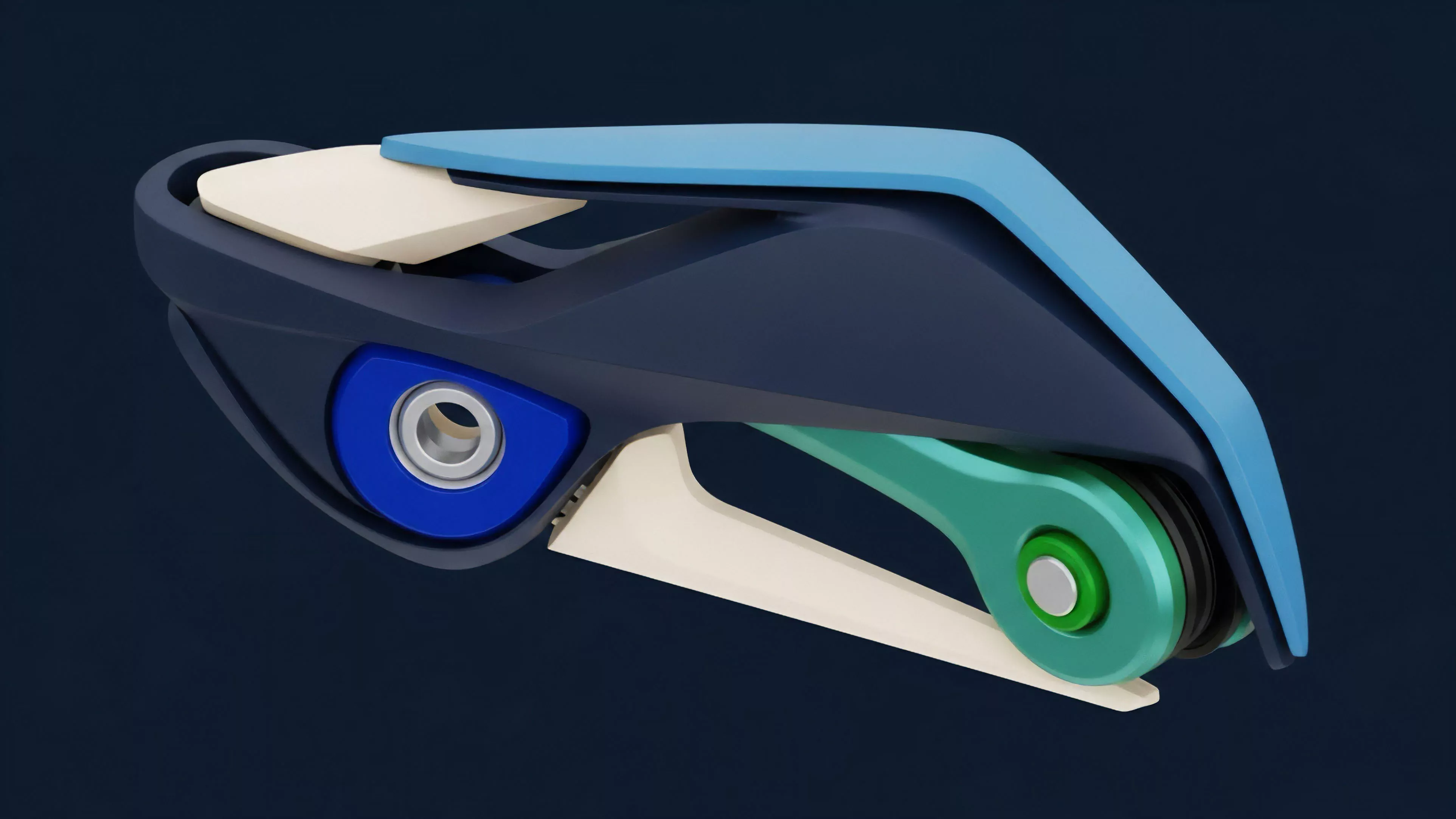
Tamper-Resistant Enclosures


Meaning ⎊ Physical device casings designed to detect and respond to unauthorized attempts to access or modify internal hardware.
Ethical Hacking Protocols


Meaning ⎊ Guidelines and procedures for security researchers to responsibly identify, test, and disclose vulnerabilities in protocols.
Threshold Cryptography Security


Meaning ⎊ The holistic security approach to protecting systems that distribute secrets across multiple parties.
Data Breach Response


Meaning ⎊ Data Breach Response provides the essential automated defense and containment architecture required to maintain solvency within volatile crypto markets.
Zeroization Protocols


Meaning ⎊ Emergency procedures to instantly and irreversibly erase sensitive data from memory when a security breach is detected.
Differential Fault Analysis


Meaning ⎊ A cryptanalytic attack that derives secret keys by comparing correct and faulty cryptographic outputs caused by system errors.
Laser Voltage Probing


Meaning ⎊ Using laser beams to non-invasively measure voltage states on microchip nodes to extract secret data or monitor operations.
Malicious Code Injection Paths


Meaning ⎊ The specific technical vulnerabilities and routes used to insert unauthorized code into a software application.
Automated Update Risks


Meaning ⎊ The danger that automatic software updates can be used to introduce malicious code into previously safe applications.
Client-Side Script Injection


Meaning ⎊ The insertion of malicious code into a webpage to execute unauthorized actions within the user browser session.
Blockchain Security Solutions


Meaning ⎊ Blockchain Security Solutions provide the essential cryptographic and procedural safeguards required to maintain integrity within decentralized markets.
Decentralized Protocol Security Audits


Meaning ⎊ Security audits provide the essential verification layer for smart contract logic to prevent unauthorized state transitions and financial loss.
Cybersecurity Risk Frameworks


Meaning ⎊ Structured guidelines for identifying, mitigating, and managing digital security risks within financial institutions.
Flash Loan Attack Detection


Meaning ⎊ Real-time identification of atomic transaction sequences designed to exploit protocol price oracles or liquidity pools.
Bug Bounty Program Efficacy


Meaning ⎊ The effectiveness of incentivizing ethical hackers to find and disclose security flaws in a protocol.
Blockchain Network Security Advancements


Meaning ⎊ Blockchain Network Security Advancements provide the essential defensive architecture required to ensure institutional-grade integrity in digital markets.
Execution Environment Hardening


Meaning ⎊ Securing infrastructure and runtime environments to reduce attack surfaces and protect sensitive financial operations.
Smart Contract Vulnerability Disclosure


Meaning ⎊ Smart Contract Vulnerability Disclosure acts as the essential governance mechanism for securing decentralized capital against code-based exploitation.
Emergency Pause Mechanism
Meaning ⎊ A safety switch allowing administrators to halt protocol activity to prevent losses during a security exploit or crisis.
Code Vulnerability


Meaning ⎊ A programming flaw in a smart contract that can be exploited to cause unauthorized access or theft of protocol funds.
