Cross Chain Data Integrity Risk


Meaning ⎊ Cross Chain Data Integrity Risk is the fundamental systemic exposure in decentralized finance where asynchronous state transfer across chains jeopardizes the financial integrity and settlement of derivative contracts.
Hybrid On-Chain Off-Chain


Meaning ⎊ Hybrid On-Chain Off-Chain architectures decouple high-speed order matching from decentralized settlement to enhance performance and security.
Cross-Chain Liquidation Engine


Meaning ⎊ The Omni-Hedge Sentinel is a cross-chain engine that uses probabilistic models and atomic messaging to enforce options-related collateral solvency across disparate blockchain networks.
Cross-Chain Margin Management


Meaning ⎊ Cross-Chain Margin Management unifies fragmented collateral across sovereign blockchains, transforming capital efficiency but introducing quantifiable liquidation latency and systemic contagion risk.
Cross-Chain Margin Engines


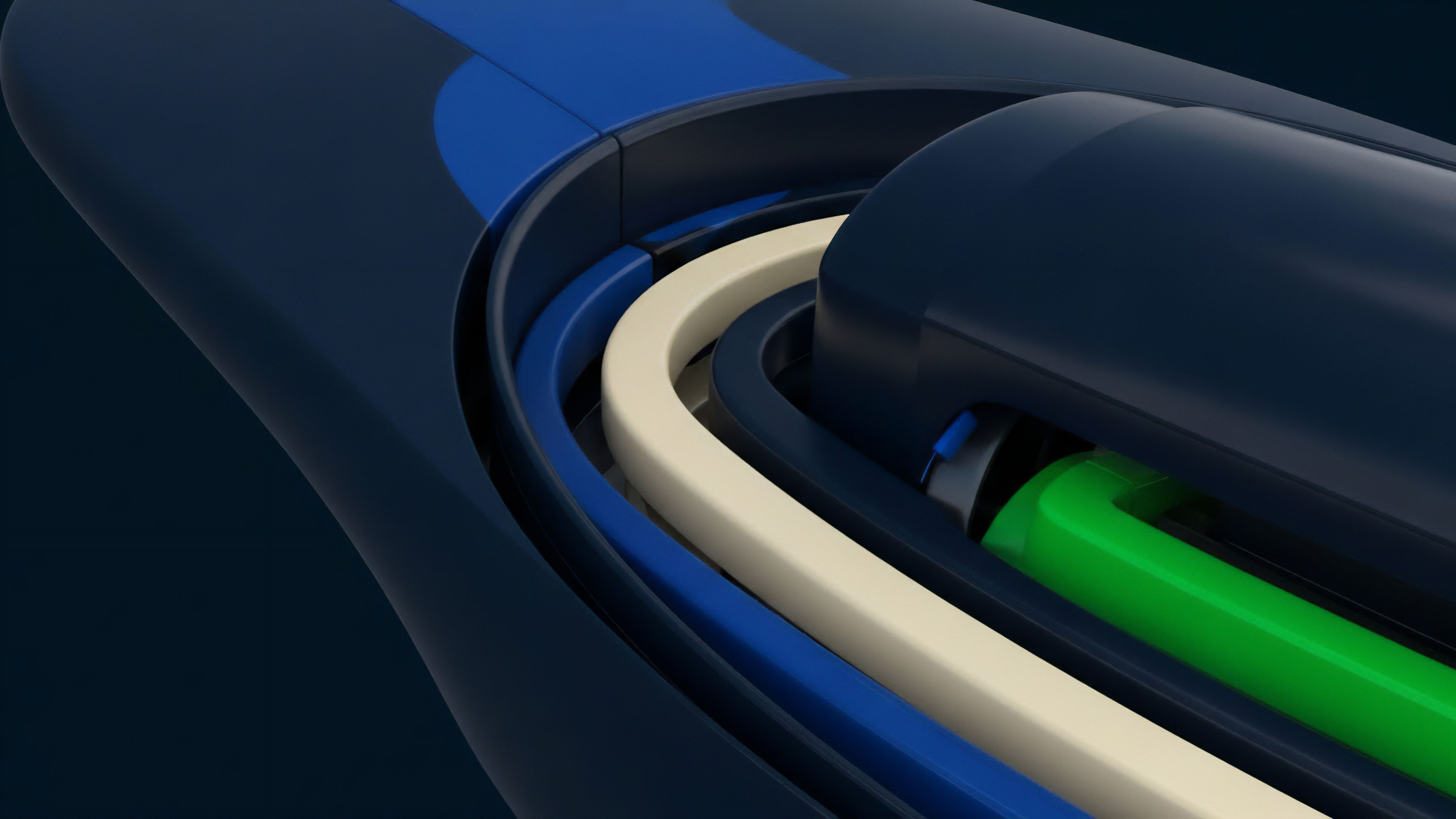
Meaning ⎊ Cross-Chain Margin Engines enable unified capital efficiency by synchronizing collateral value and liquidation risk across disparate blockchain networks.
Cross-Chain Margin Engine


Meaning ⎊ The Unified Cross-Chain Collateral Framework enables a single, multi-asset margin account verifiable across disparate blockchain environments to maximize capital efficiency for decentralized derivatives.
Cross-Chain Margin Systems
Meaning ⎊ Cross-Chain Margin Systems unify fragmented capital by creating a cryptographically enforced, single collateral pool to back derivatives across disparate blockchains.
Price Oracle Manipulation Attacks


Meaning ⎊ Price Oracle Manipulation Attacks exploit a smart contract's reliance on false, transient price data, typically via flash loans, to compromise collateral valuation and derivatives settlement logic.
Transaction Ordering Attacks


Meaning ⎊ Transaction Ordering Attacks exploit the public visibility of pending transactions to manipulate price discovery and extract value from options traders before block finalization.
Cross-Chain Compliance
Meaning ⎊ Cross-Chain Compliance ensures regulatory adherence for assets and identities across multiple blockchains, addressing state fragmentation to facilitate institutional participation in decentralized derivatives.
Cross-Chain Fees


Meaning ⎊ Cross-chain fees represent a critical friction cost in decentralized derivatives markets, impacting capital efficiency, pricing models, and systemic risk through network fragmentation.
Cross-Chain Transaction Fees


Meaning ⎊ Cross-chain transaction fees represent the economic cost of interoperability, directly impacting capital efficiency and market microstructure in decentralized finance.
Cross-Chain Feedback Loops


Meaning ⎊ Cross-Chain Feedback Loops describe the systemic propagation of risk and price volatility across distinct blockchain networks, challenging risk models for decentralized options protocols.
On-Chain Off-Chain Data Hybridization


Meaning ⎊ On-Chain Off-Chain Data Hybridization integrates external data feeds into smart contracts to enable efficient pricing and risk management for decentralized options protocols.
Cross-Chain Asset Transfer Fees
Meaning ⎊ Cross-chain asset transfer fees are a dynamic pricing mechanism reflecting the security costs, capital efficiency, and systemic risks inherent in moving value between disparate blockchain networks.
Cross-Chain MEV


Meaning ⎊ Cross-chain MEV exploits asynchronous state transitions across multiple blockchains, creating arbitrage opportunities and systemic risk from fragmented liquidity.
Cross-Chain Order Flow


Meaning ⎊ Cross-chain order flow for crypto options enables unified liquidity and collateral management across disparate blockchains, mitigating fragmentation and improving capital efficiency in decentralized derivative markets.
Liquidity Pool Attacks
Meaning ⎊ Liquidity pool attacks in crypto options exploit pricing discrepancies by manipulating on-chain data feeds, often via flash loans, to extract collateral from AMMs.
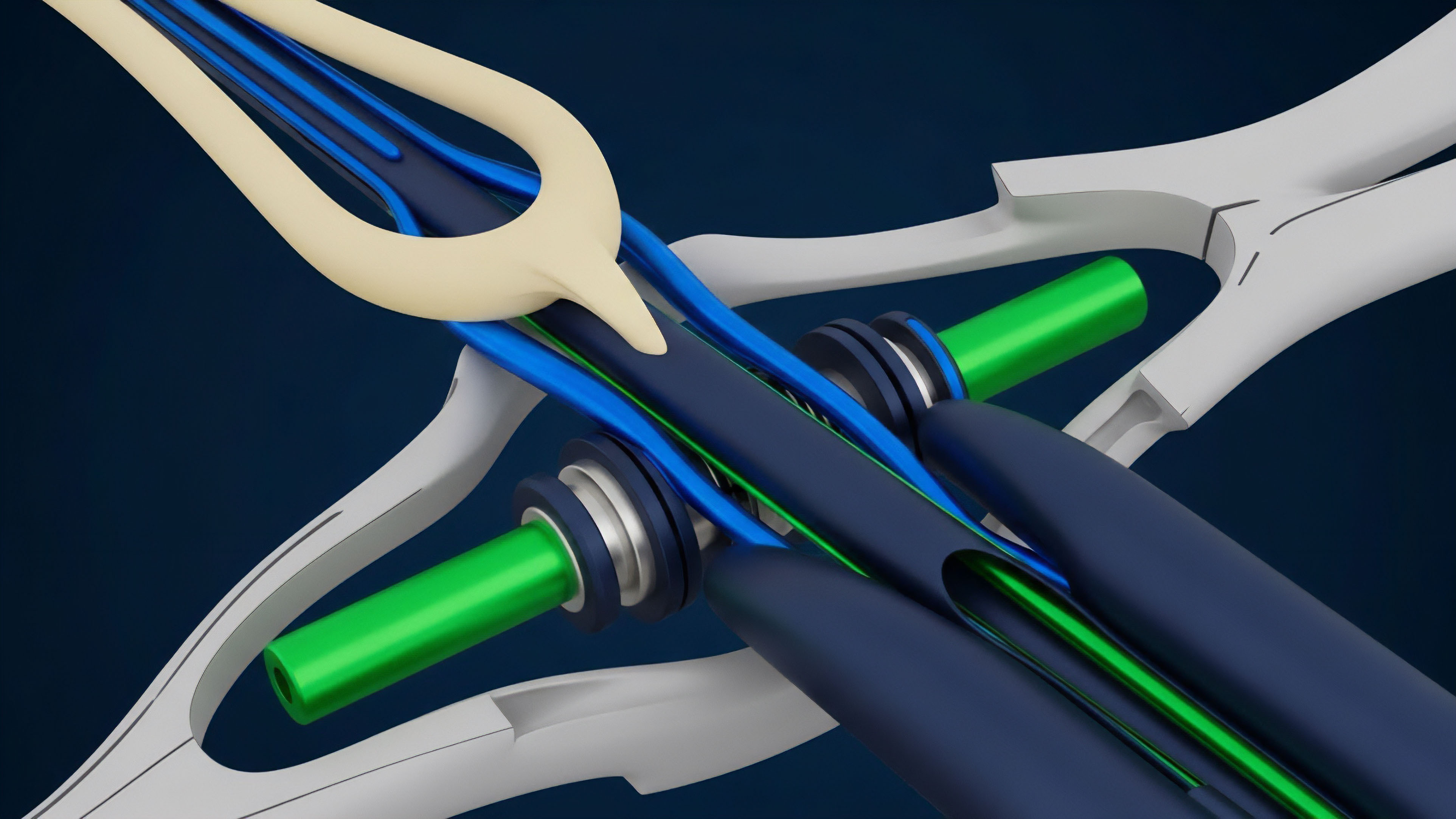
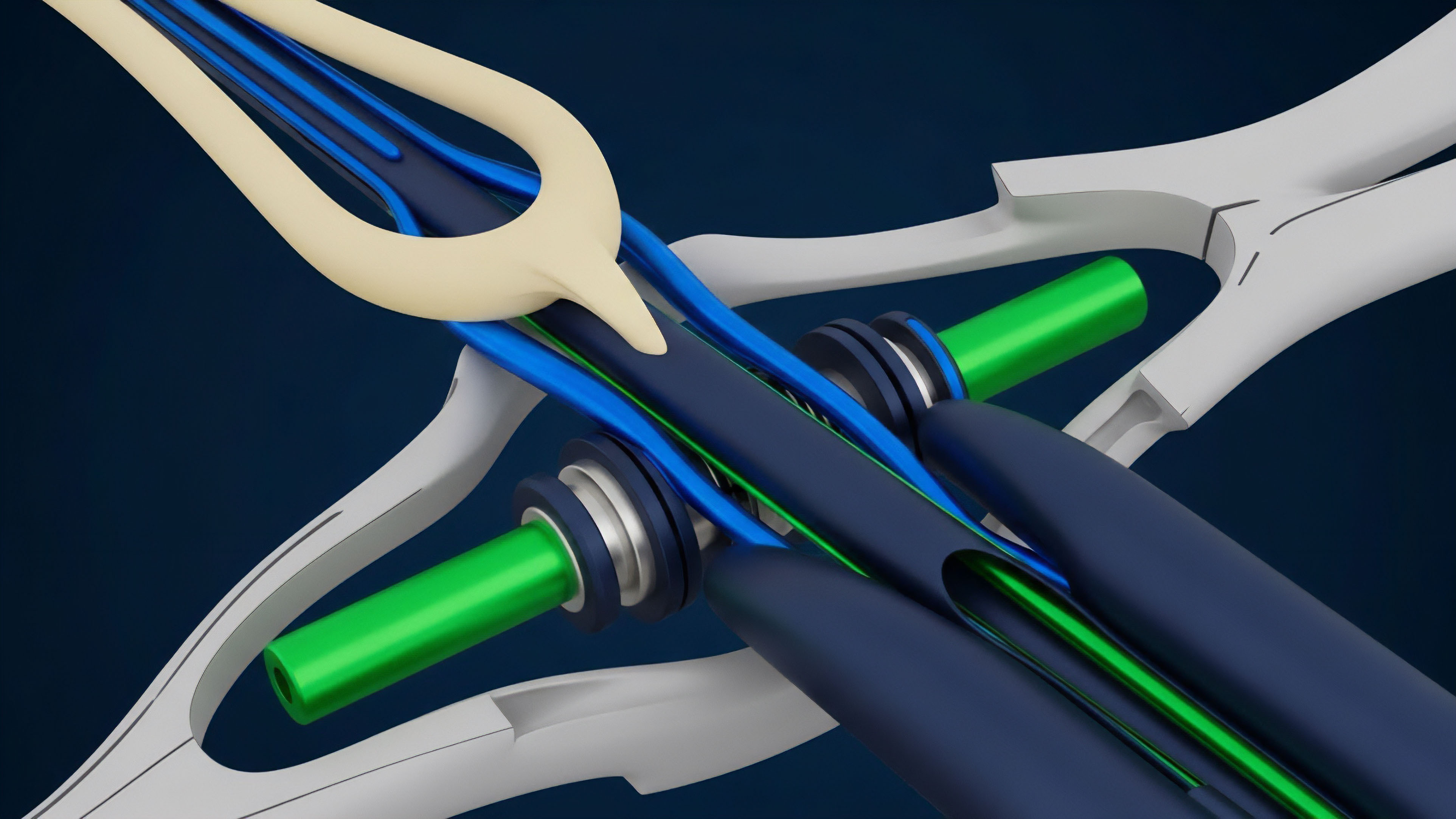
Cross-Chain Bridges


Meaning ⎊ Cross-chain bridges facilitate asset transfers between blockchains, but introduce complex security and systemic risks that impact derivative pricing and collateral integrity.
Cross-Chain Data Feeds


Meaning ⎊ Cross-chain data feeds are the essential infrastructure for multi-chain derivatives, enabling secure pricing and liquidation across fragmented blockchain ecosystems.
Cross-Chain Stress Testing


Meaning ⎊ Cross-Chain Stress Testing evaluates systemic resilience by simulating cascading failures across interconnected blockchains to assess the stability of multi-chain derivatives protocols.
Data Poisoning Attacks


Meaning ⎊ Data poisoning attacks exploit external data feeds to manipulate derivative pricing and collateral calculations, creating systemic risk for decentralized financial protocols.
Cross-Chain Bridging Costs


Meaning ⎊ Cross-chain bridging costs represent the systemic friction and security premiums that directly impede capital efficiency across fragmented blockchain ecosystems.
Cross-Chain Oracles


Meaning ⎊ Cross-chain oracles are essential for decentralized options protocols, providing accurate mark-to-market data by aggregating fragmented liquidity across multiple blockchains.
